Exploring what crypto currency is preferred on the hidden wiki and dark web? Read this guide and find out which one is the most chosen crypto for transactions and know how the crash of Cryptocurrency triggers the Crisis on the Dark Web network. So, let us read this guide and know everything in detail. The […]
The post What Crypto Currency is Preferred on The Hidden Wiki and the Dark Web? appeared first on TheHiddenWiki.
]]>Exploring what crypto currency is preferred on the hidden wiki and dark web?
Read this guide and find out which one is the most chosen crypto for transactions and know how the crash of Cryptocurrency triggers the Crisis on the Dark Web network. So, let us read this guide and know everything in detail.
The Connection Between Cryptocurrency and Hidden Wiki
There is a connection between the Hidden Wiki and crypto currency for several reasons:
1. Popularity
The Hidden Wiki and cryptocurrencies are famous on the dark web. Crypto is the main payment method that most sites on the dark net accept. Most of the sites on the dark net sell stuff to users on the internet that they will not find on the surface web.
2. Connects you to the Crypto Wallet and Mixers
Another connection between hidden wiki and crypto is that you can find hidden onion URLs linked with a crypto wallet and mixers. This directory continuously uploads new onion links under specific categories.
3. Connects to the Informational Crypto Pages
Hidden Wiki has a category of sites that lead to informational blogs. You can go through the category to find links connected to cryptocurrency blogs. Clicking on the URL will send you to the crypto informational page.
4. Leads you to the Guide that Uses Crypto
The Hidden Wiki also helps you through its informational section. It has a blog section that is useful to many beginners and guides you about the dangers of using the dark web and how you can keep yourself safe from scammers.
5. Illegal Services
Illegal marketplaces try to advantage of the reliability of the hidden wiki to gain the trust of new users and customers. It is known that illegal services on the dark web and the hidden wiki pay multiple platforms with crypto currency if the site connects its users to their marketplace.
6. Help Hidden Wiki with Crypto
This encyclopedia is basically free to use so you will not have to pay a penny to access the links on this platform. However, you can donate money to this directory to help it continue running. Many blogs and platforms on the dark web inspire their users to contribute some funds. if possible so that they can keep the servers running and offer continuous service.
Connection Between Cryptocurrency and Dark Web
The dark markets of the dark web utilize cryptocurrency as a means of payment. this hidden corner of the internet where illegal activity abounds set a new revenue record bringing a total of $5 billion in cryptocurrency in 2024.
The connection between cryptocurrency and the dark web is fixed in the shared craving for secrecy and privacy. Cryptocurrencies, with their decentralized nature and cryptographic features, including anonymity, ease of cross-border transaction, and finality of settlement offer a level of pseudonymity that aligns with the needs of dark web users. Consequently, cryptocurrencies have become the perfect vehicle for criminals to conduct their illegal activities on black markets.
The Historical Significance of this Connection
The historical status of the relationship between cryptocurrency and the dark web cannot be overstated. It has formed the route of the cryptocurrency industry and the ecosystem of the dark web and hidden wiki.
In the early days of cryptocurrency, the dark web played a crucial role in promoting its use. Silk Road marketplace made in 2011, was one of the initial prominent platforms to smooth the transactions via Crypto. Silk Road’s fame and consequent collapse brought devotion to the potentially ill use of cryptocurrencies.
Furthermore, the connection between crypto and the dark web has encouraged penetrating scrutiny from law enforcement activities and regulatory bodies all over the world. High-profile inquiries, such as the takedown of AlphaBay and Hansa Market in 2017, have uncovered the challenges establishments face in fighting illegal activities conducted via cryptocurrencies.
The Role of Crypto Currency in Hidden Wiki and Dark Web
On Hidden Wiki and the dark web cryptocurrency is the preferred means of payment. Because the crypto provides secrecy and security to buyers and sellers. The digital wallets are not associated with the user’s personal data and are used for financial transactions. That is why law enforcement can’t track the transactions and know who are the buyers and sellers.
Countless assets transferred to the dark web are considered the property of the dark web. However, these transactions are not under a nation’s government or central bank. Because these crypto transactions are pseudonymous it means that users can send and get payments without exposing their identities.
The users of Hidden Wiki and the dark web have cut back on their withdrawals to outside sources and are focusing on finding ways to spend their assets on the dark marketplaces. Users can buy and sell items and services on these marketplaces like drugs, firearms, illegal stolen goods, counterfeit, and many more.
While cryptocurrencies provide many benefits as compared to traditional payment methods including improved anonymity, transaction speeds, irreversibility, and reduced fees.
What Crypto Currency is Preferred on the Hidden Wiki and Dark Web?
The anonymous dark web marketplaces you will find on the hidden wiki directory enable illicit trade, fraud, and other serious crimes. To avoid leaving a money track that can be used in inquiries, these marketplaces depend on cryptocurrency.
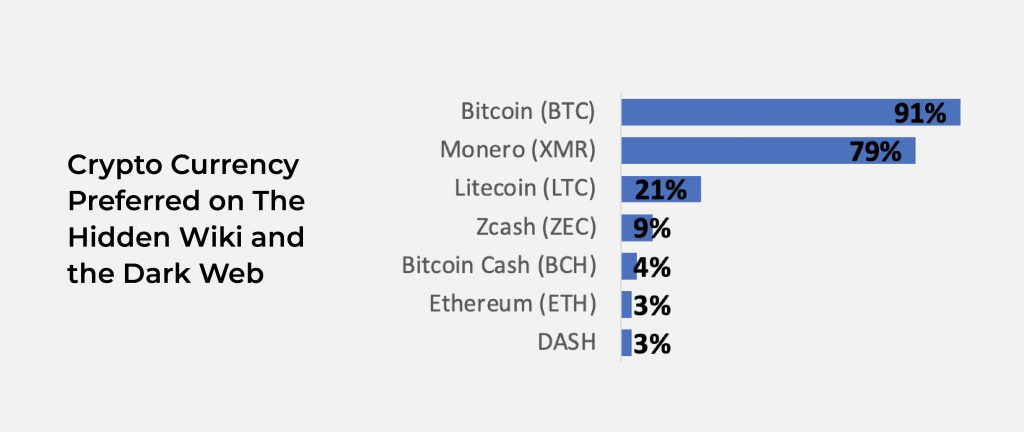
As per the analysis of almost 70 dark web markets.
- 91% accepted Bitcoin
- 79% Monero
- 21% Litecoin
- <10% accept ZCash,
- <5% Bitcoin Cash, Ethereum, or Dash.
However, the majority of the hidden wiki and dark web markets (69%) support two or more cryptocurrencies.
1. BTC: Bitcoin
Bitcoin isn’t just the most common crypto currency in the markets of the hidden wiki and dark web. This asset is broadly used on dark web marketplaces. Bitcoin can be used to purchase malware, drugs, illegal firearms, unlawful content, and other items on the dark web. It is used in money laundering to cover criminals’ tracks as well.
Many ransomware attackers also request that their victims pay their demanded ransoms in Bitcoin, making the payment less traceable from the get-go.
While Bitcoin is certainly a popular asset on the dark web, it has one glaring flaw: its pseudonymity. Bitcoin does not provide users full anonymity, as a Bitcoin wallet address can technically be used to track down the user’s identity. This process can be challenging but is possible nonetheless. Most cryptocurrencies are pseudonymous, not anonymous.
2. XMR: Monero
Unlike the majority of cryptos out there, Monero is a privacy coin. It means that it is specifically designed to keep user information private.
Monero doesn’t just hide names and contact details. If you conduct a transaction using Monero, your wallet address will also be kept private. Monero does this via stealth addresses; one-time wallet addresses that are disposed of once a single transaction is over. By using a different wallet address each time, it becomes incredibly difficult for a user to be tracked down.
Like Bitcoin, Monero has also been requested for payments by ransomware attackers on the hidden wiki and dark web. Some attackers have even offered to lower the requested ransom amount if the victim pays in Monero over Bitcoin. Again, this is likely due to Monero’s status as a privacy coin that can offer total anonymity.
All Monero users must use shielded addresses when trading XMR. Ring signatures are also used in Monero transactions, which shields public keys and transaction amounts.
3. LTC: Litcoin
Litecoin is very similar to Bitcoin in its design. The cryptocurrency and blockchain were created using Bitcoin’s source code. Because of this, Litecoin offers the same pseudonymity as Bitcoin. However, Litecoin can offer faster transaction times too, meaning users don’t have to wait hours for their payments or money movements to be processed and verified.
The same privacy as Bitcoin but faster? It’s not surprising that cybercriminals have adopted Litecoin as a form of payment on the dark web.
In the same Holland FinTech study mentioned previously, it was found that 21 percent of dark web platforms accept Litecoin payments. Litecoin isn’t nearly as popular among cybercriminals as Bitcoin and Monero, but its presence on illicit marketplaces is certainly quite solid.
Just a few years before this study, another was conducted by Recorded Future. Surprisingly, it was found here that Litecoin was the second-most popular crypto on dark web marketplaces. It seems that Monero has somewhat replaced Litecoin on the dark web over the past few years, likely due to its heightened privacy features.
4. ZEC: ZCash
Zcash is another popular privacy coin. Like Monero, Zcash allows users to conceal their wallet addresses when conducting transactions. But unlike Monero, Zcash gives you the choice of using a transparent, public address, or a shielded, private address. In this way, it’s sort of a semi-private cryptocurrency.
Either way, you can use Zcash to keep yourself anonymous, and this perk has caught the attention of malicious actors. It might be Zcash’s semi-private design that has made it less desirable among cybercriminals. After all, Monero is far more popular in general and offers the benefit of anonymity across the board.
5. BCH: Bitcoin Cash, ETH: Ethereum, or DASH: Dash
Bitcoin Cash, Dash, and Ethereum are also noteworthy examples of popular crypto currency among cybercriminals on the hidden wiki and dark web. In simple terms, the blockchain works with these three cryptos by scrambling transactions to make its users hard to trace and identify. Like Zcash, Ethereum, and Dash’s anonymity features are optional.
These assets are not used as often as the other examples listed here but still have a small presence on illicit platforms. We may see the growth of these cryptos in prevalence on the dark web, but other privacy coins, like Monero and Zcash, may soon replace them entirely.
Why do Criminals Use Crypto?
Cryptocurrencies are private they are not like traditional money where you send money to someone via bank transfer. In the traditional payment method person will be able to see your name on the transaction receipt. In addition, the person can also see other payment data, such as bank account numbers and sort codes, which are also held by many parties, like the businesses we have set up direct withdrawals. this isn’t completely dangerous; it indisputably discloses some of your personal information.
Meanwhile cryptocurrency confrontations this issue by hiding all user data within a transaction, except for the sender and recipient’s wallet address. Your name, wallet provider, and contact details are not displayed on the blockchain within the transaction details.
So, this provides a lot more privacy than traditional payment can. With crypto, you can hide your identity and other personal data when you move money around, connotation it’s harder for anybody to trail your actions.
Because of this added coat of privacy, cybercriminals now use cryptocurrency to move illegitimately used or stolen funds around. Maybe a malicious actor wants to buy drugs via crypto or subscribe to a ransomware-as-a-service platform. Even the funding of terrorist acts can be directed with cryptocurrency. Doing this with cryptocurrency lets the cybercriminals excuse law enforcement more successfully.
So, Crypto Currency Fuels the Hidden Wiki and Dark Web?
It becomes apparent if you think about how crypto fueled the growth and notoriety of the dark web and hidden wiki.
For many years the dark web and hidden wiki were just a group of extoric websites occasionally quite illegal. But nothing more than snooping for hackers and wide-ranging tech weirdos. Suppose you add a method to anonymously exchange money to a network that also strongly protects anonymity which is a recipe for big profits. When you bring money into anything it means that things will become bigger and more cultured.
Cryptocurrencies soup up the dark web and hidden wiki and lead to the development of huge black markets. However many of them are doing millions of dollars trade. That is fuel keeping the dark web and hidden wiki flourishing and thrusting.
The Crash of Cryptocurrency Triggers the Crisis on the Dark Web
The decline in the worth of cryptocurrencies has shaped a cash rush that is pushing many secretive exchanges to their breaking point. As per the research from security companies’ cybercriminals are observing to protect their stolen assets by moving them from cryptocurrencies to authorized currencies. It forced some prominent underground exchanges toward liquidation.
Operating on the dark web away from the snooping eyes of law administration, the exchanges let criminals make transactions and potentially launder their illegal gains by fluctuating the stolen funds from fiat cash to various cryptocurrencies. While paying the exchanges steep transaction charges for their pleasure. So, the exchanges hold a healthy combination of cryptocurrency and fiat money, without either being too seriously in demand. That, however, has transformed among the larger crash in cryptocurrency values.
The Report on the Crypto Crisis on the Dark Web
34 actors operating dark web exchanges in 2022 and found that none of them were promoting their platforms. Whereas many of the actors were still active on hacker forums, none of them were sponsoring their exchanges when many cryptocurrency values fell.
Despite operating underground and spreading business in cybercrime forums, launching an underground exchange is no simple job and requires important funds to get off the ground. As such, substituting the liquidated exchanges will be no easy task, particularly as cryptocurrency values continue to decline.
Actors have to build assets of numerous currencies and project mechanisms to receive payments on numerous platforms. They also have to market themselves to be uncovered and build a status so they will be right-hand.
The forum traffic is also confirming that the closures are probable to be continuing, if not permanent. The analysis noted that many of the exchange operators have also gone silent in cybercrime forums after years of almost daily postings to promote their services, signifying that a rebrand or relaunch is not planned.
Analyzer told Search Security that Generally, actors who run shops on the underground will endorse them often on forums, even daily, to ensure that people know about them. So, if they are not posting about them any longer, it means it is safe to say that they have departed.
With the exchanges going dark, it will be more problematic for cybercriminals to move their stolen money around. The researcher noted, however, that protectors should dodge getting too thrilled, as many of the major and most productive cybercrime groups will likely be able to continue operations unharmed.
These exchanges are possibly mostly used by less sophisticated actors, who will now be stuck without a way to exchange funds. The more advanced cybercrime groups have more intricate methods to exchange and launder assets and they will certainly find new methods to continue doing so.
The Future of Crypto Currency and the Hidden Wiki / Dark Web
You can argue that the golden age of crypto is well and actually ended. The big black markets have been shut down and the authorities are finding ways to cut through some of the technologies that are meant to protect the identities of users. Bitcoin in particular is not anonymous anymore.
Except for those who develop cryptocurrency, technology can stay ahead of those who want to negotiate the anonymity of the technology, we may get things shrink even more than they already have. It looks like the world is trying to purge the internet of anonymity entirely and the Dark Web and the hidden wiki are the reverse of this idea.
So, nobody knows who will win out in the end.
Sum Up
Conclusively here is a question comes out that the dark web and hidden wiki live without crypto currency. what you think about it let us know in the comment section.
The post What Crypto Currency is Preferred on The Hidden Wiki and the Dark Web? appeared first on TheHiddenWiki.
]]>The Hidden Wiki has long been regarded as the ultimate resource for navigating the depths of the hidden web like the Dark Web. It assists as a primary starting point to a world that remains hidden from the prying eyes of the surface internet. If you’re unfamiliar with the concept of the Dark Web, let’s […]
The post What is The Hidden Wiki (2024 Update for the Primary Starting Point of the Onion Underworld) appeared first on TheHiddenWiki.
]]>The Hidden Wiki has long been regarded as the ultimate resource for navigating the depths of the hidden web like the Dark Web. It assists as a primary starting point to a world that remains hidden from the prying eyes of the surface internet.
If you’re unfamiliar with the concept of the Dark Web, let’s start by shedding some light on it. And explore all the hidden gems of the hidden wiki, its legality, the relation between hidden wiki and the dark web, and why Hidden Wiki serves as the starting point for exploring the Dark Web.
The History and Evolution of The Hidden Wiki
The exact origins of the Hidden Wiki are mysterious, but it is believed to have appeared in the early 2000s. This encrypted platform started as a simple webpage with a collection of links to various hidden services on the Dark Web. It served as a centralized hub, making it easier for users to discover and access hidden services on the internet.
Over the years, The Hidden Wiki has grown to become more than just an encyclopedia. It now includes curated content, user-generated reviews, and even forums where users can discuss topics associated with the Dark Web and the hidden layers of the internet.
As the darknet rose in popularity, so did The Hidden Wiki. It extended its directory to include links to various websites, making it a central tool for users looking to discover the vast area of the Onion system. With every passing year, new sections were added, covering everything from marketplaces to forums, catering to the diverse requirements and interests of its users.
As the Hidden Wiki added traction, it also became a target for law administration agencies and hackers. Authorities have made efforts to shut down the Hidden Wiki multiple times. That leads to its periodic disappearance and comeback under different domain names. Despite these trials, the Hidden Wiki has managed to survive and continue offering access to the Dark Web.
Updates for The Hidden Wiki in 2024
As we arrive in 2024, The Hidden Wiki continues to change, adapting to the ever-changing landscape of the darknet. The latest update takes with it an assortment of new features and developments. Making it easier than ever to navigate the depths of the Onion Underworld links.
One of the key updates for The Hidden Wiki in 2024 is the enhanced user interface, making it more spontaneous and user-friendly. The addition of a search function for navigating through the site has never been easier. It allows the users to find the information they need with just a few clicks.
This new feature allows users to quickly search for specific websites or matters of interest, saving time and providing a more efficient browsing experience. Additionally, the directory has been expanded to include advanced search capabilities. That enables users to search for specific topics or keywords within The Hidden Wiki. In addition to advanced search capabilities the emerging marketplaces and forums feature. It ensures that users have access to the latest trends and developments in the darknet.
The Relationship Between the Hidden Wiki and the Dark Web

Within this hidden kingdom lies the Hidden Wiki, a website that serves as a directory of various prohibited and controversial services, forums, and marketplaces accessible on the Dark Web. The Hidden Wiki plays a crucial role in the Dark Web ecosystem. This platform is essentially a centralized hub that offers links and data about hidden services, making it easier for users to navigate the Dark Web.
The Hidden Wiki is not the only directory on the Dark Web, but it is one of the most well-known and widely used. It features a hierarchical structure, similar to Wikipedia, where users can find links to different categories of hidden services. These categories can include drugs, hacking, counterfeit documents, pornography, and more.
The Hidden Wiki also serves as a platform for individuals to share information and experiences related to the Dark Web. Through user contributions, the Hidden Wiki reflects the evolving landscape of the Dark Web, ensuring that users have access to the most up-to-date and relevant information. However, due to the nature of the Dark Web, individuals must approach the information found on the Hidden Wiki with caution and skepticism, as not all websites listed may be trustworthy or safe to visit.
So, is Using Hidden Wiki Links Legal?
The legality of using hidden wiki links depends on numerous factors, including the authority you are in and the content accessed via those links. While accessing the hidden wiki itself might not be illegal, the content you find there could hypothetically be.
Hidden wikis are known to occasionally host links to illicit activities, such as illegal drug markets, weapons sales, hiring criminals, pornography, or other criminal activities. Engaging in or accessing illegal content through these links could lead to legal consequences.
It’s vital to exercise caution and discretion when exploring the hidden wiki or any similar platforms. Make sure to follow the laws and rules of your jurisdiction and dodge accessing or engaging with illegal content.
Why Hidden Wiki Serves as the Starting Point for Exploring the Dark Web?
The primary starting point of the Onion Underworld is none other than The Hidden Wiki itself. At its core, the Hidden Wiki serves as a gateway to the Onion Underworld. But what exactly is the primary starting point of this mysterious realm?
It is the place where users start their journey into the depths of the darknet, discovering its secrets one link at a time. So if you’re considering exploring the Dark Web, The Hidden Wiki can be a dearest starting point.
When you first access The Hidden Wiki, you’ll be received with a massive collection of categories and subcategories. These categories include a wide range of topics, from hacking and cryptocurrency to alternate markets and whistleblowing platforms. Each category contains links to websites and services related to the topic. It’s vital to approach The Hidden Wiki with caution and disbelief, as not all links may be legitimate or safe.
By using The Hidden Wiki, you can lessen the risks related to unseeingly stumbling upon possibly malicious or illegal content. It’s significant to exercise caution and follow best practices to protect yourself and your digital footprint.
However, it’s crucial to understand that The Hidden Wiki is just the tip of the iceberg. Once you venture beyond its limits, you’ll encounter a vast and complex network of websites and communities, each with its exclusive offerings and risks.
Understanding the Dark Web and its Structure
The Dark Web, frequently masked in myths and misconceptions, is a part of the internet that requires special software and configurations to access. It is a haven for individuals who wish to remain unidentified and engage in activities that are yonder the reach of traditional search engines.
The Dark Web is a part of the internet that is not indexed by search engines and requires special software, such as Tor, to access. It is a realm shrouded in anonymity, where users can engage in activities that are habitually illegal or unprincipled.
This platform is often associated with illicit activities such as drug trafficking, weapons sales, and hacking services. But it also hosts legitimate content and services that prioritize privacy and security. It’s significant to note that not everything on the Dark Web is illegal. However, the lack of oversight and regulation makes it a breeding ground for illicit activity.
How to Access the Hidden Wiki Safely
Accessing the Hidden Wiki and the dark web safely requires taking several precautions to protect your identity and digital security as compared to regular browsing.
To start accessing Hidden Wiki, use the Tor browser first download, and install the Tor browser from the official website. Once installed, open the browser and enter the URL of The Hidden Wiki. This will take you to the primary starting point of the Onion Underworld, where you can start your exploration.
Here are some essential steps to consider when accessing the hidden wiki.
- Use Secure and Anonymous Software: To access the dark web, you’ll need to use specialized software like Tor. Tor routes your internet traffic via a network of volunteer-operated servers, encoding your connection and hiding your IP address. This aids preserve your secrecy and protects your identity while browsing the dark web.
- Practice Good OpSec: Operational Security, or OpSec, is vital when venturing into the dark web. Avoid using your personal information or usernames that can be traced back to your real identity. Be mindful of the data you share and take extra precautions to protect your digital footprint.
- Secure Your Device: Before accessing the dark web, make sure that your device is protected. Update your operating system and applications to the up-to-date versions, use trustworthy antivirus software, and avoid clicking on suspicious links or downloading unknown and malicious files.
- Be Cautious of What You Access: Exercise caution when accessing websites on the dark web. Avoid clicking on suspicious links or engaging with content that may be unlawful or malicious. Stick to trustworthy sources and be alert to the potential risks linked with certain activities.
4 Popular Resources Available on the Hidden Wiki
The Hidden Wiki is home to an excess of resources, each catering to a particular interest or requirement. Let’s take a closer look at some of the popular resources you can find on the Hidden Wiki directory.
- Marketplaces: One of the most well-known features of the dark web is its illicit marketplaces. These marketplaces provide a wide range of goods and services, including drugs, counterfeit documents, stolen data, and even weapons. While engaging in such activities is illegal and extremely dangerous, marketplaces on the dark web continue to flourish due to the anonymity they offer.
- Forums and Social Networks: The dark web also hosts an assortment of forums and social networks, providing a platform for like-minded individuals to connect and discuss numerous topics. These communities often rotate around sensitive subjects such as hacking, drug privacy, and anonymity. While some of these forums help as appreciated sources of data, others can be upbringing lands for illegal activities and unsafe ideas.
- Whistleblower Platforms: The dark web is not exclusively a hub for illegal activities. It also serves as a platform for individuals to secretly share sensitive information and expose wrongdoing. Whistleblower platforms on the Hidden Wiki provide a road for those seeking to shed light on exploitation, government surveillance, and corporate malpractice. These platforms offer a level of protection for whistleblowers who fear retaliation.
- Media and File Sharing: The dark web is home to many platforms that host and allot content that may be illegal or bowdlerized on the surface web. These platforms provide a means for individuals to share and access data without fear of censorship or surveillance. However, it’s vital to step carefully in this land, as engaging in illegal file sharing can have severe consequences.
Legal and Illegal Activities
While the dark web and the Hidden Wiki have gained infamy for accommodating illegal activities, it’s important to recognize that not everything on these platforms is fundamentally illegal. There are legitimate uses for the dark web, such as protecting privacy, circumventing restrictions, and easing anonymous communication.
However, it’s crucial to know that the dark web also harbors a noteworthy amount of illegal activities. Marketplaces offering drugs, fake goods, and stolen data are prevalent on the dark web, attracting both buyers and sellers. Activities such as hacking, identity theft, and cybercrime are also prevalent within these hidden corners of the internet.
It’s important to understand the legal suggestions of engaging in illegal activities on the dark web. Law enforcement agencies are actively monitoring these platforms, and the consequences for participating in or enabling illegal activities can be severe. Therefore, it’s important to exercise caution and obey the law when directing the Hidden Wiki.
The Risks and Dangers of Exploring The Hidden Wiki
While The Hidden Wiki can be an accommodating resource, it’s essential to be alert to the risks and dangers that come with exploring the Dark Web. The Dark Web is widespread with scams, malware, and illegal activities. Clicking on a malicious link or engaging with the wrong community can have severe consequences. It’s crucial to maintain a high level of vigilance, use reputable security software, and never share personal or sensitive data while browsing the Dark Web.
Accessing the Hidden Wiki and the dark web comes with essential risks. The anonymous nature of the dark web makes it an attractive platform for criminals, scammers, and hackers. It’s crucial to be aware of the potential risks and take appropriate precautions when venturing into this uncharted territory.
- Malware and Exploits: The dark web is rife with malicious actors seeking to exploit unsuspecting users. Malware, ransomware, and other forms of cyberattacks are prevalent, and accessing suspicious websites can put your personal information and devices at risk. It’s essential to have robust cybersecurity measures in place, such as using reputable antivirus software and keeping all your software up to date.
- Law Enforcement Surveillance: While the dark web offers a certain level of anonymity, it’s important to remember that law enforcement agencies are actively monitoring these platforms. Engaging in illegal activities can lead to severe legal consequences, potentially compromising your freedom and privacy. It’s crucial to understand the laws governing your jurisdiction and refrain from participating in illegal activities.
- Scams and Fraud: The dark web is teeming with scams and fraudulent schemes. From fake marketplaces to phishing attempts, criminals are constantly devising new ways to exploit unsuspecting users. It’s essential to exercise caution and skepticism when engaging in any transaction or interaction on the dark web. Verifying the legitimacy of websites and sellers is crucial to avoid falling victim to scams.
5 Tips for Navigating The Hidden Wiki Safely
While browsing The Hidden Wiki, it’s crucial to prioritize your safety and take necessary precautions. Here are some tips to help you navigate the darknet safely:
- Update your antivirus software and keep it running in the background while browsing the darknet.
- Use a virtual private network (VPN) in conjunction with the Tor browser to further enhance your anonymity.
- Exercise caution when clicking on links and only visit websites that are well-known and reputable.
- Avoid downloading files from unknown sources, as they may contain malware.
- Regularly clear your browsing history and cookies to minimize the risk of being tracked.
By following these tips, you can lessen the risks related to browsing The Hidden Wiki and explore the darknet with more peace of mind.
The Future of The Hidden Wiki
As technology advances and the darknet continues to evolve, the future of The Hidden Wiki remains uncertain. However, one thing is clear: it will continue to play a significant role in guiding users through the depths of the Onion Underworld.
With each passing year, we can expect The Hidden Wiki to adapt and recover, offering users a more seamless and secure browsing experience. As new marketplaces emerge and the darknet landscape shifts, The Hidden Wiki will continue a vital resource, serving as the primary starting point for those bold enough to venture into the unknown.
Wrapping Up
The Hidden Wiki serves as the primary starting point for exploring the depths of the Onion Underworld. With its curated list of links to numerous websites, it acts as a gateway to the darknet, offering users a glimpse into its hidden subcultures, marketplaces, and forums.
While browsing The Hidden Wiki and the darknet, it’s important to be aware of the risks and dangers associated with this kingdom. By following best practices for online security and exercising caution, you can navigate the darknet safely and unlock the secrets that lie under the surface of the web.
So, dare to venture into the unknown? Then let’s begin our journey together, as we reveal the hidden coatings of the internet and explore the enigmatic world of the Onion Underworld.
The post What is The Hidden Wiki (2024 Update for the Primary Starting Point of the Onion Underworld) appeared first on TheHiddenWiki.
]]>Do you know how easy is to visit the Hidden Wiki in 2024 to explore the dark world of the internet? In 2024, curiosity continues to drive people to experience the mysterious side of the internet. One of the fascinating destinations is the Hidden Wiki, a secret corner of the web known for its enigmatic […]
The post How Easy is it to Visit The Hidden Wiki in 2024? appeared first on TheHiddenWiki.
]]>Do you know how easy is to visit the Hidden Wiki in 2024 to explore the dark world of the internet?
In 2024, curiosity continues to drive people to experience the mysterious side of the internet. One of the fascinating destinations is the Hidden Wiki, a secret corner of the web known for its enigmatic content. But how you can easily access the Hidden Wiki in 2024? As the digital environment develops and online regulations become stricter, the hidden gem may not be as straightforward as it once was.
However, for those who successfully hide their identity, there are still ways to navigate through the shadows and discover the secrets that lie within the Hidden Wiki. In this blog post, we will uncover the existing state of accessibility to The Hidden Wiki, exploring the potential challenges that users may face and providing guidance on how to approach this hidden gem of the internet. Whether you’re a curious adventurer or a digital detective, join us as we embark on a journey to unravel the mysteries of the Hidden Wiki in 2024.
What is the Hidden Wiki on the Dark Web?
Before we dive deeply into the Hidden Wiki, let’s first understand what the dark web exactly is. The Dark web is also referred to as the black web or darknet. The dark web covers websites that are not indexed by traditional search engines like Google and more. Accessing this mysterious net requires a special browser named Tor browser. While the surface web consists of publicly visible websites and the deep web includes sites that require login credentials. However, the dark web is the hidden and unregulated part of the deep web. It is the realm of anonymity, privacy, and illegal activities that exist beyond the reach of standard internet browsing.
The Evolution of the Hidden Wiki
The Hidden Wiki has come a long way since its origin. It was initially launched as a platform for users to share information and links anonymously. It rapidly earned popularity among those seeking unconventional content. Over the years, the site has grown and developed and become an inventory for a wide range of topics, from literature to politics and technology to hacking. The Hidden Wiki, decentralized landscape, and encryption make it an attractive destination for individuals who value privacy and anonymity.
However, in 2024, the Hidden Wiki faced numerous challenges because of internet regulations. Law enforcement agencies and governments have cracked down on illicit activities taking place within its virtual walls, leading to increased investigations and attempts to shut it down. It has forced the Hidden Wiki to adapt and find new ways to maintain its presence on the internet, making it more difficult for users to access its content.
Despite these barriers, The Hidden Wiki continues to attract a dedicated community of users who are willing to put in the effort to explore its depths. Let’s take a closer look at how accessing The Hidden Wiki has changed in 2024.
How to Visit the Hidden Wiki in 2024
In earlier years, accessing the Hidden Wiki was as simple as typing in a URL and hitting the enter command. But, nowadays, the accessing process is a little bit difficult and tricky. Due to increased regulation and attempts to block its access, the Hidden Wiki now operates through a network of mirror sites and onion links.
To get into the Hidden Wiki, users must first download and install the Tor browser, a powerful tool that allows for anonymous browsing. Once the browser is installed, users can navigate to one of the many mirror sites or onion links that host the Hidden Wiki. These mirror sites serve as alternative addresses for the main site, allowing users to bypass censorship and access the content they desire.
It’s important to note that accessing The Hidden Wiki through mirror sites or onion links comes with its own set of risks and challenges. Users must exercise caution and take steps to protect their privacy and security while exploring this hidden realm of the internet.
Steps to Visit the Hidden Wiki Safely
While accessing The Hidden Wiki may seem troublesome, there are steps users can take to ensure a safer browsing experience. Here are some recommendations to consider:
- Use a reliable VPN: A VPN (virtual private network) can add extra protection of security by encrypting your internet connection and masking your IP address. It can help protect your identity and make it trickier for others to track your online activities.
- Update your security software: Keep your antivirus and anti-malware software up to date to protect against potential threats while browsing the dark web and Hidden Wiki. Regularly scanning your device for malware can help identify and remove any malicious software that may have been accidentally downloaded.
- Practice good browsing habits: When exploring the Hidden Wiki, exercise caution and be mindful of the links you click on. Avoid downloading files from unreliable sources and be doubtful of any offers that seem too good to be true. Taking these precautions can help minimize the risk of falling victim to scams or malware.
- Stay informed: Stay up to date with the latest news and developments regarding the Hidden Wiki. It can help you stay ahead of any potential risks or changes in accessibility.
By following these steps, users can navigate the Hidden Wiki with a greater extent of safety and security.
Understanding the Content on the Hidden Wiki
The Hidden Wiki is known for its wide range of content, but it’s essential to approach these onion links with caution and skepticism. As we know the decentralized behavior of the Hidden Wiki means that the quality and reliability of the information can vary greatly.
It is essential to note that this site is not a regulated website, and anyone can add or edit the onion links. This means that there is a higher risk of encountering false information, scams, or even illegal activities. Therefore, users have to pay serious attention and verify the information they come across before accepting it as accurate.
Despite that, the Hidden Wiki can also be a valuable source of unique content that may not be easily accessible through the regular web. It provides a forum for individuals to share their knowledge and perspectives on a vast range of topics. However, users who access the Hidden Wiki with an open mind and a healthy dose of skepticism can find hidden gems of information that may not be readily available anywhere.
Challenges and Risks to Visit the Hidden Wiki
Browsing the Hidden Wiki is not without its challenges and risks. As we mentioned earlier, the site has faced numerous scrutiny from law enforcement agencies, leading to shutting down and tracking its users. This means that users who visit the Hidden Wiki may be exposing themselves to potential legal consequences.
Along with the legal risk, there are also some technical challenges regarding visiting the Hidden Wiki. The use of mirror sites and onion links adds an extra layer of complications to the process, requiring users to have a basic understanding of how these tools work. Furthermore, the decentralized landscape of the Hidden Wiki means that the content can vary in quality and reliability, making it difficult for users to distinguish accurate information from misinformation.
Another challenge users may face is the presence of malicious actors on the Hidden Wiki. The anonymity provided by the Tor browser makes it an attractive platform for illicit activities, including the sale of drugs, weapons, and stolen data. Navigating through the Hidden Wiki requires caution and a keen eye for possible scams or fraudulent activities.
Legal Implications of Accessing the Hidden Wiki
While the Hidden Wiki presents a captivating gateway to the dark web, it is significant to acknowledge the fundamental risks related to this realm. The unrestricted nature of the dark web exposes users to potential threats, including cybercriminals, malware, and offensive content. For a safe and secure experience, following best practices, like avoiding unfamiliar links, maintaining strong security measures, and exercising discretion when sharing personal information is compulsory.
As technology continues to grow, so does the dark web. It is crucial to stay informed, take caution, and be aware of the potential dangers that lurk within the hidden corners of the internet. With the right knowledge and precautions, exploring the dark web can be an understanding and interesting experience, offering a glimpse into a world that exists behind the boundaries of typical browsing.
So, if you dare to venture into the depths of the dark web, remember to take every step carefully, safeguard your privacy, and embrace the mysteries that await you in the Hidden Wiki.
Staying Safe Online While Exploring the Hidden Wiki
When you visit the Hidden Wiki, it is necessary to prioritize your safety and security. By following the below-mentioned tips, you can minimize your exposure to potential risks while browsing this hidden gem of the internet.
- Limit personal information: Avoid sharing personal information or using your real name while browsing the Hidden Wiki. Maintaining your anonymity is key to protecting your privacy.
- Be mindful of your digital footprint: The sites you visit and the actions you take online can leave a digital trail. Be cautious of the information you leave behind and take steps to minimize your digital appearance.
- Regularly update your software: Keep your computer, browser, and other software up to date with the latest security patches. This helps protect against known vulnerabilities that could be utilized by malicious actors.
- Use strong, unique passwords: Avoid using the same password for multiple accounts, and consider using a password manager to store your passwords securely.
- Trust your instincts: If something feels suspicious or too good to be true, trust your gut and proceed with caution. Don’t hesitate to exit a website or close a connection if you feel uncomfortable.
11 Best Onion and Tor Sites Found on the Hidden Wiki and Dark Web
Now that you understand the precautions involved in accessing the dark web, let’s dive into the realm of the best Onion and Tor sites that the Hidden Wiki has to offer in 2024. These sites provide various needs and interests, ranging from secure communication channels to access to scientific research papers. Here are some worth exploring sites that are mentioned in 2024.
1. The Hidden Wiki
The Hidden Wiki also known as the unofficial Wikipedia of the dark web serves as a beginning point for many dark web enthusiasts. It provides an inclusive collection of onion links, giving access to various black web pages, services, and other illegal content. However, it is important to take caution while exploring this wide repository, as offensive and dangerous material may be present.
2. DuckDuckGo
It is known for its privacy-focused search engine, DuckDuckGo also offers a darknet version that acts as a private browsing tool for the dark web. While it is not a search engine typically for the dark web, DuckDuckGo’s regular site can still provide access to onion sites and dark web links when searched. It prioritizes user privacy and does not keep a log of your web activity.
3. Sci-Hub
Scientific research papers often remain behind paywalls or require substantial fees for access. However, Sci-Hub aims to bridge this gap by supplying free access to millions of scientific documents. While it provides a valuable resource for researchers and scholars, it is worth noting that accessing Sci-Hub may violate copyright restrictions in some countries.
4. ProPublica
As an award-winning non-profit news channel, ProPublica focuses on exposing abuses of power and issues of public trust. To ensure the safety of their journalists and readers, ProPublica has established a presence on the dark web. This move allows agents to anonymously share sensitive content without fear of counterattack, contributing to the fight for transparency and accountability.
5. Impreza Hosting
Deep websites need secure and anonymous hosting services and Impreza Hosting comes out as one of the most reliable options. Functioning similarly to mainstream hosting providers, Impreza Hosting offers servers, domain registration, and email hosting for black websites. It serves as an attentive and secure platform for dark web operations.
6. Tor Links
Due to the constant threat of closure faced by many Tor directories, having a backup directory becomes necessary. Tor Links serves as a unique treasure by providing a backup of “.onion” sites in case other directories go offline. It ensures that users can continue to access relevant and exclusive dark websites, even in the face of potential troubles.
7. Facebook
Facebook’s Onion version enables people in countries with restricted access to social media platforms to connect and communicate freely. While Facebook itself has faced inspection over privacy concerns, its presence on the dark web pro a lifeline for those living under repressive regimes, facilitating the exchange of information and building connections.
8. BBC Tor Mirror
In regions where access to well-known news services like the BBC is blocked, people can still stay informed through the BBC Tor Mirror. This dark web portal focuses on international affairs, ensuring that individuals living under strict censorship laws can access independent media and enhance their knowledge.
9. SecureDrop
SecureDrop plays an important role in enabling secure and anonymous file-sharing on the deep web. It offers whistleblowers a platform to submit sensitive information to media forums through a unique SecureDrop URL. Files shared through SecureDrop are automatically encrypted, protecting the sender’s identity and ensuring the safety of the information being disclosed.
10. Proton Mail
For those searching for secure and anonymous email communication, Proton Mail stands as a leading encrypted email service. Based in Switzerland, Proton Mail prioritizes user privacy and does not require personal information during the sign-up process. Its end-to-end encryption ensures that your emails remain confidential and protected from prying eyes.
11. Wasabi Wallet
Cryptocurrency followers exploring the dark web can rely on Wasabi Wallet as a trusted trading tool. It offers a secure and anonymous environment; Wasabi Wallet facilitates the buying, selling, and management of cryptocurrencies. Its robust security measures contribute to the protection of users’ financial transactions in the dark web.
Alternatives to Visit the Hidden Wiki
If you are hesitant to visit the Hidden Wiki due to its risks and challenges, there are some alternatives available. Several other sites exist that provide similar experiences while giving a higher degree of security and regulation.
- Dark Web Reddit forum: It serves as a hub for discussions and information sharing on several topics. While it may not provide the same collection of content as the Hidden Wiki it is a safe and more moderate environment for users to engage with like-minded people.
- I2P network: I2P stands for Invisible Internet Project which is similar to the Tor network. It allows anonymous browsing and access to hidden services. While it may not have the same level of hype as the Hidden Wiki, it provides a more secure and private browsing experience.
Ultimately, the choice between exploring The Hidden Wiki or its alternatives comes down to own preference and risk tolerance. It’s important to weigh the potential rewards against the potential risks and make an informed decision.
Conclusion: Is it Worth Visiting The Hidden Wiki in 2024?
The hidden wiki remains a fascinating and mysterious edge of the internet. But to visit the Hidden Wiki in 2024 is not without its challenges and risks. As the digital landscape evolves and online regulations become stricter, accessing The Hidden Wiki requires more effort and caution. Navigating through mirror sites and onion links, understanding the risks and legal implications, and taking steps to protect one’s privacy and security are all essential parts of the journey.
The post How Easy is it to Visit The Hidden Wiki in 2024? appeared first on TheHiddenWiki.
]]>Finding the legit reasons to use the Hidden Wiki in 2024? In a world where privacy and anonymity online are becoming increasingly important because of the increasing cybercrime in today’s world. Using the Dark Web and Hidden Wiki Amidst Cyber-Security Threats The Hidden Wiki has emerged as a go-to resource for users who are […]
The post Legit Reasons to Use the Hidden Wiki in 2024 appeared first on TheHiddenWiki.
]]>Finding the legit reasons to use the Hidden Wiki in 2024?
In a world where privacy and anonymity online are becoming increasingly important because of the increasing cybercrime in today’s world.
Using the Dark Web and Hidden Wiki Amidst Cyber-Security Threats
The Hidden Wiki has emerged as a go-to resource for users who are seeking a secure and discreet online experience. Whether you’re a journalist, student, or simply someone looking to protect your privacy, It offers a wide range of legitimate reasons to utilize its platform in 2024. Also, Hidden Wiki is an easy-to-use platform in 2024.
With its vast directory of hidden services, The Hidden Wiki provides access to sites that may not be easily found through traditional search engines. From anonymous communication platforms to secure marketplaces, this online platform curates a list of resources that cater to a variety of needs.
While some may question the legality and ethics of the content found on The Hidden Wiki, it’s important to note that this platform itself is not responsible for the content posted by its users. Instead, it serves as a gateway to hidden services that may otherwise be difficult to access.
In this article, we will explore the legit reasons why individuals choose to use The Hidden Wiki in 2024. By understanding the benefits and potential risks, we can make informed decisions about our online privacy and security.
What is The Hidden Wiki?
The Hidden Wiki is a website that serves as a directory of hidden services on the dark web. Unlike the regular internet, which is indexed and accessible through search engines, the dark web is a part of the internet that is not easily accessible or indexed. It requires specific software, such as Tor, to access hidden services.
The Hidden Wiki provides a list of links to various hidden services, ranging from forums and marketplaces to communication platforms and even educational resources. These services are often encrypted and offer a higher level of privacy and anonymity compared to regular websites.
However, it’s important to note that not all hidden services on The Hidden Wiki are legal or ethical. Just like the regular internet, the dark web has its fair share of illegal activities and controversial content. It’s crucial to use discretion and caution when exploring the hidden services listed on The Hidden Wiki.
Understanding the Controversy Surrounding the Hidden Wiki
Due to its association with the dark web, The Hidden Wiki has garnered a reputation for hosting illicit activities and content. While it’s true that there are illegal services listed on the platform, it’s essential to understand that The Hidden Wiki itself is not responsible for the content posted by its users.
The Hidden Wiki operates as a neutral platform, providing links to various hidden services without actively endorsing or participating in any illegal activities. It’s up to the users to navigate the platform responsibly and make informed choices about the content they choose to access.
However, the controversy surrounding The Hidden Wiki highlights the importance of using the platform responsibly and being aware of the potential risks and legal implications. It’s crucial to exercise caution and adhere to the laws and regulations of your jurisdiction while using The Hidden Wiki.
3 Legit Reasons to Use the Hidden Wiki
Despite the controversy, there are legitimate reasons why individuals choose to use The Hidden Wiki in 2024. Let’s explore some of these legit reasons to use hidden wiki:
- Privacy and Anonymity: The Hidden Wiki provides a level of privacy and anonymity that is often sought after by individuals who value their online security. By accessing hidden services through The Hidden Wiki, users can protect their identity and browse the internet without leaving a digital trail.
- Journalism and Activism: Journalists and activists often rely on The Hidden Wiki to access information and resources that may not be easily accessible through traditional channels. The platform offers a way to communicate securely and share sensitive information without fear of surveillance or censorship.
- Research and Education: The Hidden Wiki is not limited to illegal activities; it also hosts educational resources and research materials that may be difficult to find elsewhere. Researchers and academics may find value in accessing hidden services for legitimate purposes, such as studying the dark web’s impact on society or analyzing online communities.
These are just a few examples of the legit reasons why individuals choose to use The Hidden Wiki. It’s important to note that the Hidden Wiki platform itself is neutral and does not endorse or promote illegal activities. Tips For Accessing the Hidden Wiki Safely and Securely
3 Tips For Accessing the Hidden Wiki Safely and Securely

While using The Hidden Wiki can offer benefits in terms of privacy and anonymity, it’s crucial to take precautions to ensure your safety and security. Here are some tips for accessing The Hidden Wiki safely:
- Use a VPN: A Virtual Private Network (VPN) can help mask your IP address and encrypt your internet traffic, enhancing your anonymity while using the dark web or the internet in general. There are hundreds of VPNs out there but you have to choose the best of VPNs for yourself to keep your dark web journey going.
- Use Tor: Tor is software that enables anonymous communication and allows you to access hidden services on the dark web. It’s essential to download Tor from the official website and keep it updated for the latest security features.
- Verify Links: The Hidden Wiki provides links to various hidden services, but it’s crucial to verify the links’ legitimacy before accessing them. Use reliable sources and communities to cross-reference the links and ensure they lead to secure and reputable services.
By following these safety measures, you can minimize the potential risks associated with using The Hidden Wiki and enjoy a more secure online experience.
Exploring the Benefits of Using the Hidden Wiki in 2024
In 2024, The Hidden Wiki continues to offer several benefits to its users. Let’s explore some of the benefits that this site offers for its users in more detail:
- Access to Specialized Communities: The Hidden Wiki provides access to hidden services that cater to specific interests and communities. Whether you’re looking for niche forums, hobbyist groups, or support networks, The Hidden Wiki can connect you with like-minded individuals in a secure environment.
- Secure Communication: The Hidden Wiki lists various anonymous communication platforms that allow users to communicate securely without revealing their identities. These platforms can be particularly valuable for individuals who need to share sensitive information or engage in confidential conversations.
- Secure Marketplaces: While there are illegal marketplaces on the dark web, The Hidden Wiki also features legitimate marketplaces that prioritize user privacy and security. These marketplaces offer a range of products and services that may not be easily accessible through regular channels.
These benefits highlight the potential value and utility of The Hidden Wiki for individuals seeking a secure and discreet online experience to protect their privacy.
Understanding the Risks and Precautions When Using the Hidden Wiki
While The Hidden Wiki can be a valuable resource, it is essential to be aware of the risks that come with it and you must take necessary precautions when navigating the dark web:
- Illegal Activities: Engaging in illegal activities on the dark web can have severe legal consequences. It is crucial to understand and abide by the laws of your country when using The Hidden Wiki or any other dark web resources.
- Malware and Scams: The dark web is rife with malware and scams that aim to exploit unsuspecting users. Be cautious when downloading files or interacting with unknown websites, and always use reputable antivirus software.
- Law Enforcement Monitoring: While the dark web provides anonymity, it is not entirely immune to law enforcement monitoring. Governments and law enforcement agencies have dedicated resources to identify and prosecute individuals who are involved in illegal activities. Exercise caution and avoid engaging in any illicit activities that may catch the attention and get you in trouble.
- Psychological Impact: Exploring the dark web can expose users to disturbing and illegal content that may have a lasting psychological impact. It’s important to consider your mental well-being and avoid content that may be harmful.
By understanding and mitigating these risks, users can navigate The Hidden Wiki and the dark web with a greater degree of safety and peace of mind.
Navigating The Hidden Wiki on Dark Web: A Beginner’s Guide
If you’re new to The Hidden Wiki, navigating the platform can be a bit overwhelming. Here are some tips and tricks for you that will help you get started:
- Familiarize Yourself with Tor: Before accessing The Hidden Wiki, make sure you have Tor installed on your device. It’s advisable to download Tor from the official website to ensure you’re using the latest version.
- Verify Links and Services: As mentioned earlier, it’s crucial to verify the links and services listed on The Hidden Wiki before accessing them. Use reliable sources and communities to cross-reference the information and ensure you’re accessing legitimate and secure services.
- Exercise Caution: While The Hidden Wiki offers a range of legitimate services, it’s essential to exercise caution and use discretion when exploring hidden services. Be aware of the potential risks and legal implications associated with accessing certain content.
By following these guidelines, you can navigate The Hidden Wiki with greater confidence and make informed choices about the content you choose to access.
3 Tips for Using the Hidden Wiki Responsibly
Using The Hidden Wiki responsibly is crucial to ensure your safety and security, as well as to respect the laws and regulations of your jurisdiction. Here are some tips for using and accessing the Hidden Wiki safely and responsibly.
- Know the Laws: Familiarize yourself with the laws and regulations regarding the use of hidden services in your jurisdiction. Understanding the legal implications can help you make informed decisions and avoid any potential legal issues.
- Avoid Illegal Activities: While The Hidden Wiki hosts a variety of services, it’s important to refrain from engaging in any illegal activities. If you use the platform responsibly and respect the rights and privacy of others you won’t have to worry about anything.
- Protect Your Identity: Take measures to protect your identity while using The Hidden Wiki. Use pseudonyms or aliases, avoid sharing personal information, and consider using additional security measures such as encryption.
By following these tips, you can use The Hidden Wiki responsibly and minimize the potential risks associated with accessing hidden services.
The Future of The Hidden Wiki and Its Potential Impact
As technology continues to evolve, the future of The Hidden Wiki remains uncertain. While the platform currently serves as a gateway to hidden services on the dark web, advancements in technology and law enforcement may impact its availability and accessibility.
It’s important to stay informed about any developments or changes in the dark web landscape and adapt your online practices accordingly. As new platforms and tools emerge, it’s essential to evaluate their privacy and security features to ensure you can continue to protect your online privacy effectively.
How The Hidden Wiki Can Benefit Personal Privacy and Security
In an era of widespread surveillance and data breaches, personal privacy and security have become paramount concerns. The Hidden Wiki offers several benefits in this regard:
- Anonymity: The Hidden Wiki allows users to access the dark web while maintaining anonymity. By using tools like the Tor browser and VPNs, individuals can protect their identities and online activities from prying eyes.
- Encrypted Communication: The dark web offers platforms for secure and encrypted communication, protecting users from surveillance and eavesdropping. By utilizing these platforms, individuals can have private conversations and exchange sensitive information without fear of interception.
- Access to Privacy-Enhancing Technologies: The Hidden Wiki provides resources and links to privacy-enhancing technologies, such as encryption tools and secure operating systems. By exploring these resources, users can learn about and implement measures to enhance their privacy and security.
- Awareness and Education: The Hidden Wiki serves as a platform for sharing information about online security and privacy. Users can find guides, tutorials, and discussions that increase their awareness and understanding of potential threats and protective measures.
By utilizing the resources available on The Hidden Wiki, individuals can take control of their privacy and security in an increasingly digital world.
3 Alternatives to The Hidden Wiki for Accessing Hidden Content
While The Hidden Wiki is a popular platform for accessing hidden services, it’s not the only option available. Here are some alternative platforms for accessing hidden content:
- Darknet Marketplaces: Darknet marketplaces such as Dream Market and Wall Street Market offer a range of products and services that may not be easily accessible through regular channels. However, it’s important to exercise caution and verify the legitimacy of these marketplaces before engaging in any transactions.
- Onion Link Directories: Onion link directories, similar to The Hidden Wiki, provide lists of hidden services on the dark web. These directories can be a valuable resource for discovering new platforms and services.
- Private Forums and Communities: Private forums and communities on the dark web offer a more exclusive and secure environment for discussions and information sharing. These communities often require invitations or referrals to join.
It’s important to note that accessing hidden services on the dark web comes with inherent risks, and it’s crucial to exercise caution and responsibility when exploring these platforms.
FAQs
Q. How common is it to have your information on the dark web?
Data breaches can be a very common thing for you especially when you are a long-time internet user or frequent the most-used sites, your data has probably been on the dark web at some point. The best option is to check and make sure you are updated about everything related to your privacy.
Q. Is the deep web on Google?
The deep web is almost 70% of the internet that you can’t find on conventional search engines like Google it does include the dark web but also it includes sites that require sign-in like Facebook, Gmail, etc.
Q. How big is the dark web compared to the internet?
The dark web is only a small part of the internet constituting only 0.01% of the deep web, and the dark web is only 5% of the total internet.
Q. What are the different types of dark web?
Some different types of dark web include small, friend-to-friend networks, as well as large, popular networks like Tor, Freenet, I2P, and Riffle that are operated by public organizations and individuals.
Conclusion
In conclusion, Legit reasons to use Hidden Wiki in 2024 as it can offer great advantages. From privacy and anonymity to a platform that caters to various needs of an average user. However, it’s important to acknowledge the controversy surrounding The Hidden Wiki and the potential risks associated with accessing hidden services. Responsible usage, adherence to laws and regulations, and a cautious approach are necessary to navigate the platform safely and securely.
As technology continues to evolve, it’s essential to stay informed about the latest developments in the dark web landscape and evaluate the pros and cons of using platforms like The Hidden Wiki. By making informed decisions, we can protect our online privacy and security while leveraging the benefits that such platforms offer
The post Legit Reasons to Use the Hidden Wiki in 2024 appeared first on TheHiddenWiki.
]]>Cybercriminals on the dark web use deepfakes to generate AI fake videos and images for illegal activities, including fraud, blackmail, stealing confidential data, stock manipulation, sextortion, and other crimes. In this post, we will let you know all the missuses of deepfakes technology that are used on dark web marketplaces. But let us first know […]
The post The Danger of Deepfakes Use Cases on Dark Web in the Future appeared first on TheHiddenWiki.
]]>Cybercriminals on the dark web use deepfakes to generate AI fake videos and images for illegal activities, including fraud, blackmail, stealing confidential data, stock manipulation, sextortion, and other crimes.
In this post, we will let you know all the missuses of deepfakes technology that are used on dark web marketplaces. But let us first know about deepfakes, how they work, and the technologies that are used in deepfakes.
| Key Takeaways Deepfakes use GANs: Generative adversarial networks, NLP: Natural language processing, and CNNs: Convolutional neural networks, high-performance computing, and autoencoder AIs to accomplish their work. Deepfakes are synthetic media files, including imagery, video, or audio, that manipulate and replace another person’s face or voice. The developers of deepfakes on dark web charges from $300 to $20000. However, the charges are based on the complexity of the work. Deepfakes can be easily recognized as fake by analyzing the reflection of light in the eyes, blurring around the ends of the face, lack of blinking and the irregularities in the hair, mood patterns, scars, etc. |
An Overview of Deepfakes
The term Deepfakes combines with two words deep learning and fake. Deepfakes are basically synthetic media files, including imagery, video, or audio. It typically features a specific individual who manipulates and replaces another person’s face or voice.
However, this work is accomplished using generative AI: artificial intelligence-powered neural networks, also known as GANs: generative adversarial networks. It processes data, creates patterns, and learns much like the human brain does.
The deepfake technology was developed at the beginning of the 1990s by researchers at academic institutions. Industries recently adopted this technology for adding visual effects and animation. Right now, the extensive availability of computer science technology and the growing accessibility of AI enable virtually anyone to make highly realistic fake content.
In fact, the number of deepfake videos is growing by 900% a year. The manipulation of content to influence audiences is not new. But the line between what is real and what is fake has become razor-thin.
How Deepfakes Work?
Deepfakes basically use 2 algorithms to create and refine fake content.
- Generator: It built a training data set based on the desired output for creating the initial fake content.
- Discriminator: It analyzes how realistic or fake the initial version of the content is.
However, the procedure is repeated to let the generator progress at producing realistic content. At the same time, the discriminator becomes more skilled at spotting flaws for the generator to be accurate. The amalgamation of generator and discrimination algorithms makes a generative adversarial network.
GAN uses deep learning to recognize patterns in the real image and then use those patterns to produce the fake image. The GAN system views the image and video from various angles to capture all the details and perspectives like behavior, movement, and speech patterns when producing a video and an image.
Different Approaches for Creating Deepfakes
Here, we have shared some specific approaches for creating deepfakes.
- Audio Deepfakes: GAN duplicates the audio of a person’s voice and creates a model based on the vocal patterns. Then, uses the model to take the voice and say anything the creators want for deepfake audio with the help of NLP. The video game developers basically use this approach.
- Video Deepfakes: A neural network-based deepfake autoencoder analyzes the content to get relevant attributes of the target, like facial expressions and body language, for creating a video. Then, it executes these features onto the original video.
- Lip Syncing: The recurrent neural networks map a voice recording to the video, making it look like the person in the video is speaking the words in the recording in lip-syncing deepfake.
Computing Technologies Required to Create Deepfakes
Because of the following technologies, creating deepfakes is becoming easier, more precise, and more relevant.
- GANs: Generative adversarial network technology is used to develop the deepfake content using the generator and discriminator algorithm.
- NLP: Natural language processing is used to produce deepfake audio. The algorithm of NLP technology analyzes the attributes of a target speech and then produces original text via those attributes.
- CNN: Convolutional neural networks analyze patterns in visual data that are used for facial recognition and movement tracking.
- High-performance Computing: This technology offers the necessary power required to generate deepfakes.
- Autoencoders: This technology detects the relevant features of a target, like facial expressions and body movements, and then executes these features onto the source video.
The Missuses of Deepfakes Technology on the Dark Web
Deepfake technology has some positive points, as it is used in generating music videos, caller-responsive services, and customer support. In addition to these uses, the negative points easily overwhelm our society. Below, we have shared the misuse in the dark web world of deepfake technology.
1. Spreading Fake News
Currently, fake news is disruptive because of its prevalence and influence over the public. Deep fake tech helps its users to make more credible hoax material than ever, like fake speeches and interviews involving celebrities, politicians, and influential figures to spread misinformation and fake news to manipulate the public.
2. Cyber Attacks
New technology always brings about new solutions — and that includes crime. The recent trend in deepfakes could bring online criminality to a new level. Consider that this technology will become more available as time advances. So, it will become a standard AI tool for social engineering (which is already one of the most effective cybercriminal techniques). Social engineering relies on human emotions as it is the weakest link in the digital security chain for manipulating a person’s behavior to make them do something they would usually avoid.
3. Sextortion
This technology is also used to create fake adult and sexually explicit material featuring the victim person without their consent, violating their privacy and dignity. This scam is known as sextortion, which is a common thing in dark web forums. Because of deepfaking, it has become very easy to replace and change a face and voice to another one in a video. Dreadful but accurate, you would never spot a single difference till you are told. It is so easy that any video alteration is possible, including yours and me.
4. Phishing Attacks
Deepfakers can use this technology for a new brand of phishing attacks. A phisher can mimic someone else to encourage new victims into action. For instance, a video could be generated with a CEO announcing that a company has lost all customer data. However, everything can be on point with the deepfaked voice or video. An attacker could sell the data of the company on the dark web and deep web marketplaces, and on the contrary, the victim could lose the company.
5. Blackmailing and Bullying
The common example of blackmailing and bullying is when a target image is put in an illegal, inappropriate, or otherwise compromising situation, such as lying to the public, engaging in explicit sexual acts, or taking drugs with the help of deepfaking technology. These videos are used to extract a victim, collapse a person’s reputation, get revenge, or simply cyberbully them. The most usual blackmail or revenge use is nonconsensual deepfake adult content, also known as revenge porn.
6. Fraud
Deepfakes are also used to impersonate or defame an individual, organization, or brand to obtain identifiable information such as bank accounts and credit card numbers. This can sometimes include impersonating executives of companies or other employees with credentials to access sensitive information and creating fake reviews and testimonials, which is a major cybersecurity threat.
7. False Evidence
Deepfakes involve the assembly of false images or audio that can be used as evidence of implying guilt or innocence. In a legal case, these deepfakes are so good that even the prosecution may not be able to decipher the real ones from them. It led them, in many cases, to try introducing them as evidence at trial. And because of their genuine form, it can be very difficult for defense lawyers to verify that the evidence is dishonest.
8. Stock Manipulation
Deepfakes materials are used to affect a company’s stock price. For example, a fake video of a chief executed officer making damaging statements about the company could lower its stock price. A fake video about a high-tech advance or product launch could increase a company’s stock. Furthermore, they could release a deepfake video of the organization’s CEO making a positive statement about technological inventions to progress the company’s stock. They could also release a video with damaging content to lower the company’s stock price.
9. Fake Identity
There are thousands of pseudo-accounts created using photographs from deepfakes. Anonymous users create deepfake non-existent pictures with prominent and use fictional names with the intention of hiding their identity. The users then actively engage in forums and discussions where they incite people with propaganda. Others use the accounts to dupe unsuspecting users to lure them into online scams.
The Danger of Deepfakes on the Dark Web
According to reports, deepfakes employee burnout and ransomware attacks from the dark web. The forums of the dark web discuss deepfakes generating its services, methods, lessons, and news of evolving tactics and technology. These discussions are largely concentrated in English- and Russian-language criminal forums. But related topics were also observed on Turkish-, Spanish- and Chinese-language forums.
However, the most common deepfake-related topics on dark web forum services are editing videos and pictures, how-to methods and instructions, requirements for best practices, sharing free software downloads and photo generators, general interests, and announcements on advancements in deepfake technologies. Moreover, there is a strong surface web presence and interest in deepfake technology, consisting of open-source deepfake tools, dedicated forums, and discussions on popular messenger applications such as Telegram and Discord.”
Here, we have shared some cyberthreat activities using the deepfake that we found on the dark web.
- A threat actor offered services on hack forums of the dark web for $20 per minute of fraudulent video with realism.
- The developers of deepfakes on dark web charges from $300 to $20000 based on the complexity of the work.
- Another threat actor posted their willingness to pay $16000 for deepfake services, including video and photo editing.
- An anonymous researcher stated that almost 244625 videos had been uploaded to the top adult websites of the dark web that were set up from deepfake technology.
- The survey of 125 cybersecurity incidents stated that the security incidents involving deepfake use in the dark web have risen in the last year.
- Criminals from the dark web often request deepfakes for cryptocurrency scams, cracking online accounts, or adult content.
Future of Deepfakes
Currently, deepfakes technology is in its infancy, but it lets the cybercriminals on the dark web harm others severely. It can be easily recognized as fake; here are a few examples of recognizing the deepfakes.
- The reflection of light in the eyes
- Blurring around the ends of the face
- Lack of blinking in eyes
- Irregularities in the hair, mood patterns, scars, etc.
However, machine learning and artificial intelligence technology are quickly maturing and increasingly becoming more difficult to detect. That is why the imperfections will disappear over time as the software used to produce deepfakes improvises hastily.
There are many wits from technology companies trying to combat deepfakes. It will be a constant struggle till companies finally outplace deepfake creators who, more often than not, can quickly find new ways to stay ahead of detection methods and continue to cover their tracks.
Summing UP
The dangers of deepfakes on the dark web lie in the potential to get misused for malicious purposes. That can include spreading fake news, cyberattacks, sextortion, fake identity, stock manipulation, blackmailing, bullying, and other cybercrimes. Furthermore, bad actors can use this technology to make fake videos of people saying or doing things they never actually said or did.
The dark web world is filled with service methods, lessons, and news of evolving tactics and technology for generating deepfakes and charges a huge amount for services. Thousands of people use these services for such cyber-attacks.
The post The Danger of Deepfakes Use Cases on Dark Web in the Future appeared first on TheHiddenWiki.
]]>Struggling to find the best VPN for safe Hidden wiki and deep web use? That too which are tested and are safe to use services in 2024. What is a VPN (Virtual Private Network)? In order to find the best here, we have given a little introduction to what a VPN is. A VPN, or […]
The post The Best VPNs for Safe Hidden Wiki and Deep Web Use, 2024 Tested Services appeared first on TheHiddenWiki.
]]>Struggling to find the best VPN for safe Hidden wiki and deep web use? That too which are tested and are safe to use services in 2024.
What is a VPN (Virtual Private Network)?
In order to find the best here, we have given a little introduction to what a VPN is.
A VPN, or a Virtual Private Network, is a networking technology we use every day. It is to protect our privacy and anonymity online. This creates a tunnel that is a bridge between our connection to the internet, and all online traffic that passes through this tunnel is encrypted. In simple words, a VPN works like a filter that will turn your data into gibberish. And will make your data completely useless for the cybercriminal.
We use a VPN to mask our IP address to browse safely on Hidden Wiki and the deep web. Especially when using the Deep/Dark web or the Hidden Wiki, it is important to use a VPN to conceal your identities and get an untraceable address that is provided by the VPN service.
Types of VPNs
There are different types of VPNs, and we have mentioned three main types for you to be familiar with:
- SSL VPN
- Site-to-site VPN
- Client-to-Server VPN
Simple Tips on How to Surf Securely With a VPN
A VPN (Virtual Private Network) encrypts your activities on the web, which can only be decoded with the help of a key. Only your PC and the VPN would know about this key. Especially when you want to access the safe Hidden Wiki and Deep web you must use VPN. Only your PC and the VPN would know about this key. So, your IP address won’t be recognized. Furthermore, different VPNs use different encryption processes, and they generally function in three steps.
- First, you have to be online, then start your VPN. Now, the VPN acts as a secure tunnel between you and the internet. Your ISP and other third parties cannot detect this tunnel of yours.
- Your device is now on the local network of the VPN, and your IP address can be changed to an IP address provided by the VPN server.
- Then, you will be able to surf the internet at will, as the VPN protects all your data.
Using VPN for Hidden Wiki and Deep/Dark Web
To access the Dark web, one must need a special search engine like Tor (Tor Onion Browser) using a VPN with it gives it extra privacy and anonymity. And allows everyone to keep their privacy secured; however, it can be used by many for illegal activities and to prevent illegal activities as well.
Using a VPN for privacy in the Tor browser is the best way to access the dark web safely and securely. A dark web VPN prevents websites and your ISP from knowing your identity or the fact that you are using the dark. It can be a good practice generally but particularly important in countries where the Tor browser is blocked, such as China, Turkmenistan, Russia, and Belarus.
The List of Best VPNs for Browsing Hidden Wiki and Deep Web Safely
Here, we have mentioned some of the best VPN services that you can use to Browse Safe Hidden Wiki and Deep Web.
1. NordVPN
NordVPN is a VPN service provided by Nordsec Ltd with applications for Microsoft Windows, macOS, Linux, Android, iOS, and many more. Manual setup for the VPN is available for wireless routers, NAS devices, and other platforms. NordVPN also has a no-logs policy and 256-bit AES encryption to avoid the invasion of privacy.
The market-leading encryption and secure tunneling protocols in this VPN ensure that your data is safe and that all servers run on RAM, as they are extremely useful and are restarted every time the data gets wiped out. There is no information available for anyone to steal. Many of the NordVPN servers use this technology.
2. PrivateVPN
The fastest-growing Private VPN worldwide. You can stay private and enjoy the entire internet at lightning speeds with the safest and most affordable VPN provider. It offers 256-bit AES encryption for robust internet data security, and it also offers a sufficient balance between speed, versatility, and privacy. This VPN also performs well with stable connections and also successfully unblocks streaming platforms like Netflix.
3. Surfshark
It is a cybersecurity company focused on developing human privacy and security solutions. Surfshark VPN is reliable. It has received praising reviews from leading experts in the field. It offers 3,200+ servers in over 60 countries, and it also has 256-bit AES encryption. Surfshark has advanced features that are perfect for Tor to keep your online anonymity intact and your activities hidden. With multi-hop servers, it provide greater anonymity and privacy. It also helps the one to keep it protected and secure from IPv6, DNS, and WebRTC leaks and also comes with a kill switch.
4. TOTALVPN
It is a rare and good private VPN service that combines security and convenience. Which also offers excellent apps and an impressive selection of servers from all around the world. However, it lacks some high-end features and was slow in our tests. TOTALVPN also offer 50 plus VPN servers. It is the best choice if you want to protect your device from malware, invasive ads, hackers, and other cyber threats.
5. ULTRAVPN
This VPN hides your IP address, online activity, and location from all websites and online services. The UltraVPN is registered outside of the US. Moreover, it is known for its anti-privacy laws and has an explicit zero-logs policy. It hides your IP address, online activity, and locations from online services. Also, it can connect 10 devices at a time and has servers in 125 locations globally while protecting your data.
6. IP VANISH
This was founded in 2012 by Mudhook Media Inc., an independent subsidiary of Highwinds Network Group in Orlando, Florida. IPVanish directs the internet traffic of its users through remote servers. Furthermore, it also helps in concealing the user’s IP address and encrypting data transmitted through the connection. Users can simultaneously connect an unlimited number of devices.
It provides unbreakable encryption, a no-log policy, and leak protection. It also has an “obfuscation feature” that masks the user’s encrypted VPN tunnel as regular internet traffic. However, if you are thinking of purchasing it, keep in mind that this VPN, unfortunately, does not accept payment in Bitcoin.
7. Express VPN
It is a VPN service that offers privacy and security software that encrypts users’ web traffic and conceals their IP addresses. Moreover, it is also registered in the British Virgin Islands as Express Technologies Ltd. As of September 2021, ExpressVPN is now owned by Kape Technologies and reportedly has 4 million users. The security is due to the modern encryption of 4,096-bit DHE-RSA, 256-bit AES keys with SHA512 authentication, and perfect secrecy. It also has nodes in 90+ countries with over 3,000 fast servers.
8. Norton VPN
This VPN is incredibly fast, works well enough, and is simple. It doesn’t have many advanced features, like unblocking or privacy-protecting abilities, to match the top VPN competition, but it’s good value when bundled with other Norton services. It has AES-256 encryption and has a strict no-logging policy.
Norton also adds security tools like Wi-Fi security and ad blocker. It also has servers in 29 different countries, including the United Kingdom, the United States, and Brazil. However, it does not allow you to choose specific servers manually.
9. CyberGhost
This VPN encrypts your online traffic and masks your real IP address, whether you’re streaming, gaming, shopping, banking, or simply browsing on the deep web. No one will know who you are or would be able to find your real location. The CyberGhost is usable in Windows, MacOS, Linux, iOS, and Android, and you can also connect up to 7 devices simultaneously. It has more than 6,500 VPN servers present in 80+ countries worldwide. This VPN also adheres to a 45-day money-back policy.
10. Atlas VPN
This VPN is a freemium VPN service provider with applications for Microsoft Windows, macOS, Android TV, Linux, Android, iOS, Amazon Fire TV, and Apple TV. Moreover, this online VPN includes a tool that blocks malware, third-party trackers, and ads. It has a strict no-log policy and secures your data using AES encryption. The kill switch and split tunneling help the VPN and separate it from the regular traffic. Also, it can boast over 750 servers in more than 40 locations from all over the world.
11. Bitdefender VPN
This VPN allows digital privacy & freedom, making it as easy as flicking on a light switch. Furthermore, it also Banks, streams & downloads without exposing a single byte of personal information. Bitdefender’s paid plans also offer over 4,000 servers in over 50 countries.
However, the only catch is that it has a 10-device limit, which isn’t that bad. It offers VPN security protocols like Kill switch and split tunneling. Its payment plan is $2.92 per month and $30.00 per year.
12. IVACY
This VPN stands out as a noteworthy platform that offers impressive features at a fair price. It also has different subscription plans and pricing for accessibility and ensures customer satisfaction. This is also the best free VPN for Chrome Extension as it unblocks websites, streams videos & downloads anonymously via our top-rated global servers. It provides 5700+ servers; however, the speed can be an issue, but it is 100% safe.
Features of a Good VPN
As we rely on VPNs to perform tasks when browsing, here are some of the things that you should know when trusting a VPN:
- The basic primary job of a VPN should be to hide your IP address from ISPs and other third parties, which will allow you to send and receive information without any risk that anyone would see it.
- A good VPN should also prevent you from leaving traces behind, like on your internet, search browser history, or your cookies. It is important to avoid any third party gaining access to your data or financial, or any confidential information and other content on websites.
- One of the good features of a VPN is that it detects any sudden downtime and terminates the preselected programs, reducing the likelihood that data is compromised.
- A strong VPN also ensures the privacy of the person and checks on everyone who tries to log in. Like when you enter the password, a code will be sent to your mobile device, which makes it impossible for third-party apps to access your secure connection.
FAQs
Q. Are you safe on the dark web?
The dark web has its risks and cons, which one should be aware of before and while accessing and browsing on the platform.
Q. Can your IP address be traced on the dark web?
Yes, an individual’s internet activity can be tracked on the dark web using their IP address; that’s why it requires a VPN service provider.
Q. Is it illegal to use the Onion browser?
The Tor Onion is totally legal to use and browse. However, some of the illicit acts there are illegal and horrendous.
Q. Is Tor censored in Australia?
There are no laws in Australia against Tor or the dark web in general. However, if you use these platforms for committing illegal activities then you can be prosecuted.
Q. Is google safer than Tor?
Google is a more convenient option for everyday browsing, which people prefer, whereas the Tor Browser is the winner when it comes to privacy and security.
Conclusion
When it comes to online browsing, it is important to make sure that you protect your privacy and security; however, when you access the dark web through the Tor browser, it is very important to mask and conceal your identity so it won’t be easy for cybercriminals to track you down. Therefore VPN (Virtual Service Provider) helps you to conceal your IP address. Therefore, we have mentioned a list of the best VPN services that you can download to access the safe hidden wiki and deep web.
The post The Best VPNs for Safe Hidden Wiki and Deep Web Use, 2024 Tested Services appeared first on TheHiddenWiki.
]]>Do you often take part in giveaways while online shopping? You know that usually, stores offer free services and some discounts on their selective products in the name of giveaways. But the recently launched dark web market for carding site BidenCash on the Hidden Wiki announced a huge giveaway of 1.9 million stolen cards. In […]
The post The Dark Web Market Present on The Hidden Wiki Goes Ballistic with a Huge Giveaway appeared first on TheHiddenWiki.
]]>Do you often take part in giveaways while online shopping? You know that usually, stores offer free services and some discounts on their selective products in the name of giveaways. But the recently launched dark web market for carding site BidenCash on the Hidden Wiki announced a huge giveaway of 1.9 million stolen cards. In these cards, you will get the data leaks for free to gain the title of the top carding shop among threat actors.
The Unique Dark Web Market on Hidden Wiki
Businesses usually provide discounts and promotional codes when celebrating their big event. BidenCash has offered its unique version of the blastic giveaway in the form of stolen personal financial details. They provide cardholder’s full names, credit card numbers, and bank information. For any seasoned hacker, this vulnerable information is a treasure when it comes to facilitating digital transactions.
The term carding is used to express the kind of credit card fraud where a stolen credit card is used to charge prepaid cards. By buying a prepaid gift card, fraudulent can cover their tracks, engage in money laundering, and use personal information in abusive ways.
There are two segments of the carding marketplace: they sell data in a text format. It includes the cardholder’s name, card number, and the card’s expiration date. The second method is in the form of card dumps, which are details that have been derived from the card’s magnetic stripe.
As a successive player in the cybercrime economy, BidenCash empowers bad actors to use these stolen credit cards to cover their illegal activities. There are two methods to steal this sensitive piece of information: data-stealing malware and point-of-sale devices.
Furthermore, this data contains credit card information from all over the world. The US card holders are on the radar and usually most affected by these cyber attacks. Moreover, China, Mexico, India, and UK credit card details are also sold on the dark web.
What Type of Information does this Marketplace Sale
Cybercriminals will use this type of rich information grab to target innocent people with additional attacks. The stolen data in underground online forums and the dark web market is known as fullz; you will find it on Hidden Wiki. On those platforms, cybercriminals purchase and sell stolen personal details. Fullz refers to the set of complete and fundamental information belonging to unsuspecting victims. Cybercriminals commonly use this set of complete information for fraudulent activities, like identity theft, credit card fraud, and other financial scams. The set of information known as Fullz includes:
- Full name of a person
- Date of birth
- Social security number
- Complete address
- Phone number
- Email address
- Bank account details
- Credit card information
- Other personally identifiable details
With the help of this precious information, cybercriminals can open fraudulent accounts under victim names and make unauthorized transactions.
The Hidden Wiki Goes Ballistic with a Huge Giveaway on the Dark Web Market
The BidenCash stolen credit card marketplace has announced the giveaway of 1.9 million for free to promote their store to cybercriminals. The latest giveaway from bidenCash includes credit and debit card credentials in plain text. But unlike the site’s old leaks, it does not include the names and emails of cardholders. BidenCash, the well-known dark web carding marketplace, has leaked over 1.9 million valid payment card details, including debit and credit card data, on a notorious Russian language cybercrime and hacking forum. In June 2023, the same forum offered the sale of military satellite access for $15,000.
The overall figure for leaked card details is 1.9 million. Upon deduplication, the accurate figure is reduced to 1.6 million cards. It was worth highlighting that on March 2023, BidenCash giveaway 2 million card details as part of its first-anniversary celebration. The leak consists of the full names of cardholders, bank details, card number and their expiration dates, CVV numbers, home addresses, and more than 500,000 email addresses.
Cyble, the cybersecurity researchers confirmed that the files contained over 2,165,700 bank cards, especially it contained 740,857 credit cards, 811,676 debit cards, and 293 charge cards. The largest piece, 965,846, belongs to United States card owners, here we mentioned the country name and number of victims.
| Country Name | Number of Cards |
| United States | 965,846 |
| Mexico | 97,665 |
| China | 97,003 |
| United Kingdom | 86,313 |
| Canada | 36,906 |
| India | 36,672 |
| Italy | 23,009 |
| South Africa | 22,798 |
| Australia | 21,361 |
| Brazil | 19,700 |
On the other hand, this time, the leak doesn’t include the names or email addresses of the card owners. Instead, the leaked details include the full payment card number, expiry date, and CVV numbers in a plain text format. However, the expiration date of most cards ranges between 2025 to 2029, but few cards expire in 2023.
The latest leak is the fourth credit card dump the carding shop has released for free since October 2022. With the previous leaks, the number of cards was 1.22 million, 2 million, and 230,000 stolen cards. It contains a total of over 5 million stolen cards leaked for free.
History of BidenCash
bidenCash is known as a hub for stolen credit and debit card data. It is operating on both the dark web and the clear net.BidenCash marketplace that you will find on Hidden Wiki. It was established in April 2022, following the seizure of other card markets and carding platforms by the Russian authorities. Since its existence, it has been grabbing the attention of both new and experienced cybercriminal customers.
After it was re-established in June 2022, BidenCash started a promotional campaign that consisted of sharing a dump of 8 million lines of stolen data for sale, including thousands of stolen credit cards. Since then, it has continued its work by utilizing the dumping method. It involves daily listings of stolen credit card data on the site and frequently dumping heavy amounts of stolen credit card information at the same time. It sells these credit card details for just as little as $0.15.
The Bidencash administrators use multiple web skimmers and info-stealer malware to collect both regular and dump-related listings. Only after one week, the website announced another promotional campaign to celebrate its first anniversary. This celebration time, the site dumped over 2 million stolen card data, and this time, it was free of cost.
Promotional Giveaways are not New in the Carding Sites
On the dark web marketplace, BidenCash is not the one who offers ballistic giveaways. The old criminal carding marketplace of the dark web that you will find on the hidden Wiki is known as AllWorld Cards. It posted on numerous hacking forums where they provided one million leaked credit cards for free. According to the reports, these credit cards were stolen between 2018 and 2019.
The threat actor addressed that a random sampling of 98 cards showed a minimum of 27% of the cards were still active. However, the report of D3Labs (an Italian security firm) shows that 50% of cards are still valid.
Cybersecurity firm Cyble also analyzed this credit card dump and states that the leak includes the full name of the cardholder, card numbers, expiration dates, CVV numbers, countries, states, cities, addresses, zip codes, email, and phone numbers for every credit card.
The Allworld cards site launched in May 2021 and has a huge listing of 2,634,615 credit cards. The country with the most cards is the U.S., with 1,167,616 cards for sale. Cards details range between $0.30 to $14.40, with 73% of the credit cards costing between $3 to $5. This site owner aims to be a big player and with this one million free dump. They will likely grab many other threat actors’ attraction to their card shop.
While Cybele has only analyzed 400,000 cards, the top five associated credit cards are as follows:
| Bank Name | Number of Cards |
| State Bank of India | 44,654 |
| JPMorgan Chase Bank N.Y | 27,440 |
| BBVA Bancomer S.A | 21,624 |
| The Toronto Dominion Bank | 14,647 |
| Poste Italiane S.P.A (Banco Posta) | 14,066 |
BidenCash vs. The Dark Web Competition
On February 15, 2021, when Joker’s Stash officially closed, various card marketplaces of the dark web will also be found in hidden Wiki attempting to earn the title of top card marketplace. Telegram-based card shops are increasingly conquering market share from more traditional web-based card shops. Currently, BidenCash is a mid-to-top-tier card marketplace in terms of volume and popularity among threat actors.
This shop has managed to regularly increase the volume of cards sold through its platform throughout 2022. They offered giveaways of free credit cards, which is the real reason behind its huge popularity among bad actors.
BidenCash was established on April 27, 2022, shortly after Russian authorities took action against several illegal card shops. That includes Forum, Trump Dumps, and UniCC, along the Sky-Fraud, which is the carding forum and remote desktop Protocol access shop UAS. These cybercrimes-related takedowns represent one of the last crack-downs of Russian authorities in the cybercrime world before its military 2022 invasion of Ukraine. It represents significant movements in the market of credit card shops as new and emergent card shops in the illegal landscape.
How Threat Actors Obtain Data and Utilize It
Card-not-Present
Card fraud commonly falls into two categories: card-not-present and card-present. Card-not-present fraud relies on breached financial data that is being sold and circulated on the dark web marketplace that you will find on the hidden Wiki, illegal forums, and chat services. Card-not-present fraud allows bad actors to be in control of a large number of compromised cards and credentials to fund unauthorized purchases. Furthermore, they can resell the stolen data to other carders. Who then leverage the exposed information most frequently through card cloning or online shopping account linking.
This information is generally leaked when a threat actor obtains data that is accidentally leaked. Doing with a code repository and misconfigured network device, financial details, and other personally identifiable information (PII) on unsecured websites and bank login information. However, they implement targeted skimming and shimming attacks against ATMs and POC systems. It is usually at gas stations where credit and debit card payments are accepted.
Card Present
Card-present fraud requires the bad actor to present a fake or stolen card to the merchants physically. This method has an obvious hazard that card-not-present fraudsters are not at risk of getting caught or the card being declined. This step is much more difficult for the bad actor selling card details or using them to make off with fraudulently buying goods and services. Card-present fraud has been typically overshadowed by card-not-present activity. However, it is still a present risk to retailers and financial institutions.
Malware
Some kinds of malware are specially made for data exportation or logging. These include remote access Trojans (RATs), which allow an attacker to make a remote connection to exfiltrate data and theif. These are (RATs) that can steal sign-in credentials, cookies, payment card numbers, and other browser-stored information.
Ransomware
Extortionist ransomware attacks blackmail the victim organization with the sale of private and sensitive details to get them to pay for the liberation. Ransomware gangs understand that retailers store sensitive customer data, including financial data. These could be precious both in negotiations and in the resale of the information on the dark web market on the hidden Wiki.
Credential Stuffing
Credential stuffing attacks, which include brute force attacks, refer to multiple techniques. It relies on testing a huge number of username and password combinations against sign-in infrastructure. Threat actors who carry out these kinds of attacks mostly do so to gain unauthorized access to poorly secured banks, e-commerce, or other type of accounts. They usually test the validity of compromised data before selling them on the dark web.
How to Protect Yourself from Cyber Attack
Cardholders should keep an eye on charges made to their accounts and immediately report any suspicious activity to their bank. Adding an extra layer of protection, such as validating certain purchases and setting up charging limits where possible. These were excellent ways to prevent cybercriminals from using stolen payment cards. Some banks also offer virtual cards that users can recall easily or one-time cards that are deleted automatically after making one purchase.
Final Words
In the dark web market on the hidden Wiki, BidenCash has emerged as a top-tier carding site on the darknet. This shop offers a wide range of stolen credit and debit card information for just as little as $0.15. However, to gain popularity and earn the title of top carding site, the marketplace announced huge giveaways periodically.
The post The Dark Web Market Present on The Hidden Wiki Goes Ballistic with a Huge Giveaway appeared first on TheHiddenWiki.
]]>In a world where information is just a click away, it’s hard to imagine that there may be a hidden wiki realm lurking beneath the surface of the internet. But hidden internet search engines exist, offering a mysterious and intriguing alternative to traditional search engines. However, with this allure comes a host of safety concerns […]
The post Navigating Hidden Internet Search Engines: Safety and Awareness appeared first on TheHiddenWiki.
]]>In a world where information is just a click away, it’s hard to imagine that there may be a hidden wiki realm lurking beneath the surface of the internet. But hidden internet search engines exist, offering a mysterious and intriguing alternative to traditional search engines.
However, with this allure comes a host of safety concerns and potential risks that you need to be aware of. How can you navigate these hidden search engines safely? What steps can you take to protect your privacy and ensure your data is secure?
Join us as we unravel the secrets of navigating hidden internet search engines and delve into the realm of safety and awareness.
The Hidden World of Internet Search Engines
Discover a whole new realm of search engines that are hidden from the average internet user. These search engines operate on the deep web, also known as the dark web. Unlike popular search engines like Google and Bing, these hidden search engines provide access to websites and content that aren’t indexed by traditional search engines.
The deep web is a vast and mysterious part of the internet that isn’t easily accessible through regular means. It requires specialized software and knowledge to access these hidden search engines.
One of the most well-known hidden search engines is called Tor, which stands for The Onion Router. Tor allows users to browse the internet anonymously by encrypting their traffic and bouncing it through a network of relays. This makes it extremely difficult for anyone to track your online activities.
Another hidden search engine is called Freenet, which is decentralized and censorship-resistant. Freenet users can access websites and content without worrying about government censorship or surveillance.
These hidden search engines have gained popularity among individuals who value privacy and anonymity online. However, it’s important to note that the deep web is also home to illegal activities and content. Therefore, it’s essential to exercise caution and use these hidden search engines responsibly.
Understanding the Risks of Hidden Search Engines
Hidden search engines come with inherent risks that users must be aware of. While these search engines may offer certain benefits, such as anonymity and access to restricted content, they also expose users to numerous dangers.
One of the main risks is encountering illegal or harmful content. Since hidden search engines aren’t regulated like mainstream search engines, they often index websites that contain illegal activities, such as drug trafficking, hacking, and child exploitation. This means that users may inadvertently stumble upon disturbing or illegal content while conducting searches.
Another risk is the potential for malware or viruses. Hidden search engines are notorious for hosting websites that distribute malicious software. These websites may trick users into downloading harmful files or expose them to phishing attacks, leading to identity theft or financial loss.
Additionally, hidden search engines can be a breeding ground for cybercriminals. Hackers and scammers often exploit the anonymity provided by these search engines to carry out illegal activities, such as selling stolen credentials or conducting fraudulent transactions.
Therefore, users must exercise caution and be aware of the risks associated with using hidden search engines.
Privacy Concerns and Protecting Your Data
- It’s essential to take proactive measures when using hidden search engines to protect your data and address privacy concerns.
- While hidden search engines offer anonymity and privacy, it’s important to remember that they aren’t foolproof.
- To safeguard your data, start by using a reputable virtual private network (VPN). A VPN encrypts your internet connection, making it difficult for anyone to intercept your data.
- Additionally, consider using a browser that prioritizes privacy, such as Tor or Brave. These browsers have built-in features that block tracking cookies and prevent websites from collecting your personal information.
- Another way to protect your data is by being cautious about the information you share online. Avoid providing unnecessary personal details, and be mindful of the websites you visit.
- Lastly, regularly clear your browsing history, cookies, and cache to minimize the amount of data stored on your device.
Navigating the Dark Web: Tips and Precautions
When exploring the Dark Web, it’s crucial to take certain precautions to ensure your safety and security. The Dark Web is notorious for being a hub of illegal activities, such as drug trafficking, hacking, and the sale of stolen data. There are several tips and precautions you should keep in mind when you browse this hidden part of the internet.
First and foremost, it’s essential to use a reliable and reputable VPN (Virtual Private Network). A VPN helps to encrypt your internet traffic and mask your IP address, making it harder for anyone to trace your online activities. Additionally, always use Tor, the most common browser for accessing the Dark Web. Tor provides anonymity by bouncing your internet connection through multiple servers, making it difficult to track your online presence.
Furthermore, exercise extreme caution when interacting with unknown websites or individuals on the Dark Web. Avoid clicking on suspicious links or downloading files from untrusted sources, as they may contain malware or viruses. Remember to disable JavaScript in your browser settings to minimize the risk of being targeted by malicious code.
Lastly, it’s crucial to maintain your anonymity by refraining from using personal information or real names when creating accounts or participating in discussions on the Dark Web. Be aware that law enforcement agencies actively monitor the Dark Web, and your activities could have serious consequences if you engage in illegal activities.
How to Access Hidden Search Engines Safely
There are a few tips you should keep in mind to access hidden search engines safely,
- First, make sure you’re using a reliable and secure VPN to protect your identity and encrypt your internet connection.
- Second, be cautious of the risks involved in using hidden search engines, such as encountering illegal content or malicious websites.
- Lastly, always exercise caution and discretion when accessing the hidden web to ensure your online safety and privacy.
Safe Access to Hidden Search Engine Tips
For a safer way to access hidden search engines, consider using a VPN or Tor network. These tools can help protect your privacy and ensure secure browsing.
- A VPN (Virtual Private Network) creates a secure connection between your device and the internet, encrypting your data and masking your IP address. This makes it difficult for anyone to track your online activities.
- Tor, on the other hand, is a network that routes your internet traffic through a series of volunteer-operated servers, making it nearly impossible for anyone to trace your online activities back to you.
- By using either a VPN or Tor network, you can browse hidden search engines without leaving a digital footprint and minimize the risk of your personal information falling into the wrong hands.
Stay safe and protect your privacy while exploring the depths of the internet.
Hidden Search Engine Risks
To safely access hidden search engines, it’s important to be aware of the risks involved and take necessary precautions. These hidden search engines, also known as the dark web, pose several risks that can compromise your online safety.
One major risk is encountering illegal content, including drugs, weapons, and stolen data. Additionally, hidden search engines may expose you to malware and hacking attempts, as they often lack the security measures found on regular search engines.
To mitigate these risks, you should use a virtual private network (VPN) to encrypt your internet traffic and protect your identity. It’s also crucial to keep your antivirus software up to date and avoid clicking on suspicious links.
Uncovering the Truth: Fact-checking on Hidden Search Engines
When it comes to fact-checking on hidden search engines, you need reliable methods to separate truth from fiction.
Evaluating the credibility of sources is crucial in uncovering the truth. By using reliable fact-checking techniques and critically analyzing the sources, you can ensure that the information you find on hidden search engines is accurate and trustworthy.
Reliable Fact-Checking Methods
Hidden search engines offer reliable fact-checking methods to uncover the truth. When using these search engines, you can rely on various mechanisms to verify the accuracy of information.
One effective method is cross-referencing. By comparing information from multiple sources, you can identify inconsistencies or discrepancies that may indicate false or misleading information.
Another useful technique is utilizing reputable fact-checking organizations. Hidden search engines often collaborate with trusted organizations that specialize in fact-checking. These organizations assess the accuracy of claims made in online content and provide unbiased evaluations.
Additionally, hidden search engines employ advanced algorithms and artificial intelligence to analyze and verify information. These technologies can detect patterns of misinformation and flag suspicious content.
Evaluating Credibility Sources
Evaluating the credibility of sources is crucial when fact-checking on hidden search engines. With the vast amount of information available, it can be challenging to determine what sources are reliable and trustworthy. There are a few key factors to consider to ensure you’re getting accurate information.
- First, examine the author’s expertise and credentials. Look for individuals who’ve relevant qualifications or experience in the subject matter.
- Second, check for citations and references within the content. Reliable sources often provide evidence to support their claims.
- Third, consider the reputation of the website or platform hosting the information. Reputable sites typically have a history of providing accurate and unbiased content.
- Lastly, cross-reference the information with other reliable sources to verify its accuracy.
Exploring the Deep Web: What You Need to Know
If you’re curious about the deep web and want to know what you need to explore it, we’ve got you covered.
The deep web refers to the part of the internet that isn’t indexed by traditional search engines like Google. It consists of websites and content that aren’t easily accessible to the general public.
To explore the deep web, you’ll need a few things. First, you’ll need a special browser, such as Tor, which allows you to access websites with .onion domains. This browser provides anonymity and encryption, making it harder for anyone to track your online activities.
Second, it’s important to be cautious and aware of the potential risks associated with exploring the deep web. While there’s a wealth of information available, there’s also a darker side to the deep web, with illegal activities and malicious content. It’s crucial to exercise caution and use good judgment when navigating these hidden corners of the internet.
Lastly, keep in mind that the deep web is constantly changing, so it’s important to stay updated on the latest tools, techniques, and safety measures to ensure a secure and informative exploration.
Hidden Search Engines Vs. Traditional Search Engines
It’s important to consider the unique features and capabilities that each offers in order to understand the differences between hidden search engines and traditional search engines,
Traditional search engines like Google, Bing, and Yahoo are designed to index and display content from the surface web, which is the portion of the internet that’s easily accessible and can be found through regular search queries. These search engines use web crawlers to scan and index web pages, making them highly efficient at retrieving information from millions of websites.
On the other hand, hidden search engines focus on indexing content from the deep web, also known as the dark web. Traditional search engines don’t index this part of the internet and require specialized software, such as Tor, to access. Hidden search engines like Torch, Grams, and Ahmia are specifically designed to navigate this hidden realm and provide users with access to websites, forums, and other resources that aren’t available through traditional search engines.
One of the main differences between hidden and traditional search engines is the level of anonymity and privacy they offer. Hidden search engines are often used to access content that may be illegal or sensitive, and they prioritize user privacy and security. They also employ encryption and anonymization techniques to protect user identities and ensure that browsing activities remain hidden.
In terms of search results, traditional search engines prioritize popular and frequently visited websites, while hidden search engines focus on providing access to more obscure and hard-to-find content. This can be particularly useful for researchers, journalists, and individuals who require access to specialized information that isn’t readily available on the surface web.
Tips for Conducting Effective Searches on Hidden Engines
Make your searches on hidden engines more effective by using specific keywords and refining your search queries. When using hidden search engines, it’s important to understand that they operate differently from traditional search engines. These hidden engines index a wide range of websites that aren’t accessible through regular search engines, making it crucial to use targeted search terms to find the desired information.
To conduct an effective search on hidden engines, start by using specific keywords that accurately describe what you’re looking for. Avoid using generic terms that may yield irrelevant results. Instead, be as precise as possible when formulating your search query. For example, if you’re searching for information about cybersecurity, use keywords like ‘dark web cybersecurity’ or ‘hidden internet security’ to narrow down your search.
Furthermore, refining your search queries can greatly enhance the effectiveness of your search. Use operators such as AND, OR, and NOT to specify your search criteria. For instance, if you want to find articles on hidden internet security but exclude any information related to hacking, you can use the operator NOT followed by the term ‘hacking’ in your search query.
Staying Safe and Aware: Best Practices for Hidden Search Engine Usage
When using hidden search engines, it’s important to prioritize your safety and awareness by following best practices.
First and foremost, make sure to use a reliable and trustworthy VPN (Virtual Private Network) to protect your online identity. A VPN encrypts your internet connection, making it difficult for anyone to track your online activities.
Additionally, remember to clear your browsing history and cookies regularly to minimize the chances of your search history being tracked or stored.
Another important practice is to be cautious of the websites you visit. Hidden search engines can lead you to the dark web, where illegal activities and malicious content can be found. Exercise caution and avoid clicking on suspicious links or downloading unknown files. It’s crucial to keep your antivirus software up to date to protect yourself from potential malware or viruses.
Furthermore, it’s essential to be mindful of the information you share online. Avoid providing personal information or engaging in sensitive conversations on hidden search engines. Remember that your privacy is paramount, and sharing too much information can put you at risk.
Lastly, always trust your instincts. If something seems too good to be true or feels unsafe, it’s best to exit the website or search immediately.
FAQs
Q. Can Hidden Search Engines Be Accessed Using a Regular Web Browser?
Yes, hidden search engines can be accessed using a regular web browser. Just type in the URL of the hidden search engine into the address bar and hit enter. It’s that simple!
Q. Are Hidden Search Engines Legal to Use?
Yes, hidden search engines are legal to use. However, it is important to exercise caution and be aware of the potential risks associated with these platforms, as they may host illegal content.
Q. How Can I Protect My Personal Information While Using Hidden Search Engines?
To protect your personal information while using hidden search engines, make sure to use a reliable VPN, avoid entering sensitive data on suspicious sites, and regularly update your antivirus software for added security.
Q. What Precautions Should I Take When Accessing the Dark Web?
When accessing the dark web, be cautious. Use a secure VPN, avoid downloading suspicious files, and don’t share personal information. Stay vigilant and remember that your safety is paramount.
Q. Are Hidden Search Engines More Effective Than Traditional Search Engines in Finding Specific Information?
Hidden search engines can be more effective than traditional ones in finding specific information. They allow you to access a vast amount of content that is not indexed by regular search engines, expanding your search capabilities.
Conclusion
In conclusion, navigating hidden internet search engines requires a strong understanding of the risks involved and the importance of privacy protection. By following safety precautions and being aware of the dark web’s potential dangers, you can access hidden search engines safely. However, it’s essential to note that hidden search engines differ from traditional ones, and effective searches on these platforms require specific strategies. By staying vigilant and practicing best practices, you can ensure a safer and more informed experience while using hidden search engines.
The post Navigating Hidden Internet Search Engines: Safety and Awareness appeared first on TheHiddenWiki.
]]>Imagine a vast and mysterious realm hidden beneath the surface of the internet, a place where anonymity reigns and boundaries blur. Welcome to the Deep Web, a realm that holds both fascination and danger. Within this enigmatic landscape lies a hidden gem known as the Hidden Wiki. But before you embark on this journey, it […]
The post Understanding the Hidden Wiki Onion: Risks and Precautions appeared first on TheHiddenWiki.
]]>Imagine a vast and mysterious realm hidden beneath the surface of the internet, a place where anonymity reigns and boundaries blur. Welcome to the Deep Web, a realm that holds both fascination and danger. Within this enigmatic landscape lies a hidden gem known as the Hidden Wiki.
But before you embark on this journey, it is crucial to understand the risks and precautions that come with exploring its depths. From illegal activities to cyber-attacks, this discussion will shed light on the potential dangers that lurk within while providing essential is to safeguard your identity and privacy.
Brace yourself, for the Hidden Wiki holds secrets that demand your attention.
The Deep Web: An Overview
The Deep Web offers a vast and hidden realm of online content, accessible only through specific software or configurations. It’s a part of the internet that can’t be indexed by search engines like Google or accessed through regular web browsers. Unlike the surface web, which is the portion of the internet that’s easily accessible and visible to everyone, the Deep Web remains hidden and secure.
One of the main reasons for the Deep Web’s obscurity is the use of encryption and anonymity tools such as Tor (The Onion Router). Tor allows users to browse the internet anonymously by routing their connection through a series of volunteer-run servers. This not only conceals the user’s identity but also their location and browsing activity.
Within the Deep Web, you can find a wide range of content, both legal and illegal. Some of the legal content includes academic databases, private forums, and government resources. However, it’s important to note that there’s also a darker side to the Deep Web, where illegal activities such as drug trafficking, hacking services, and counterfeit goods can be found.
It’s important to take precautions to access the Deep Web safely. This includes using reputable software like Tor, keeping your operating system and browser up to date, and being cautious of the websites you visit. It’s important to remember that while the Deep Web offers a wealth of information and resources, it also poses risks and potential dangers.
Unmasking the Hidden Wiki
Unveiling the Hidden Wiki reveals a vast network of interconnected websites on the Deep Web. This underground directory serves as a gateway to various hidden services, offering users a glimpse into the obscure corners of the internet. By accessing the Hidden Wiki, you can find links to websites that aren’t indexed by traditional search engines. These websites cover a wide range of topics, from forums and marketplaces to illicit activities and controversial content.
However, it’s important to exercise caution when exploring the Hidden Wiki. While it can provide access to valuable information and resources, it’s also a breeding ground for illegal activities and malicious content. Many of the websites listed on the Hidden Wiki are involved in illegal trades, such as drugs, weapons, and stolen data. Additionally, there’s a risk of stumbling upon disturbing or explicit content that can be emotionally distressing.
It’s crucial to take certain precautions to protect yourself while navigating the Hidden Wiki. Firstly, ensure that you’re using a secure and anonymous connection, such as the Tor browser. This will help protect your identity and maintain your privacy. Secondly, exercise skepticism and verify the legitimacy of websites before accessing them. Lastly, be mindful of the legal implications and potential risks associated with engaging in any illegal activities or accessing explicit content.
Risks of Accessing the Hidden Wiki
Before you access the Hidden Wiki, it’s important to be aware of the risks involved.
- One major risk is the potential for your privacy and anonymity to be compromised, as accessing the deep web can expose your identity to surveillance.
- Additionally, there’s a high chance of encountering illegal content, which can have serious legal consequences.
- Lastly, accessing the Hidden Wiki increases the likelihood of falling victim to cyberattacks, as the deep web is known for being a breeding ground for malicious activities.
Privacy and Anonymity Risks
It’s essential to be aware of the potential dangers that come with exploring this hidden online realm. To understand the privacy and anonymity risks associated with accessing the Hidden Wiki on the Deep Web
When accessing the Hidden Wiki, you expose yourself to various privacy risks. The Deep Web operates outside the boundaries of traditional search engines and is known for hosting illegal activities, such as drug trafficking and cybercrime. By accessing the Hidden Wiki, you may unintentionally expose your personal information to hackers and law enforcement agencies.
Moreover, the use of Tor, a tool often used to access the Deep Web, doesn’t guarantee complete anonymity. Government agencies and skilled hackers can still potentially track your online activities. It’s crucial to take preventive measures, such as using a virtual private network (VPN) and employing strong encryption methods, to protect your privacy and maintain your anonymity when navigating the Hidden Wiki on the Deep Web.
Exposure to Illegal Content
When accessing the Hidden Wiki on the Deep Web, you expose yourself to the inherent risks of being exposed to illegal content. The Deep Web is known for its anonymity and lack of regulation, making it a breeding ground for illegal activities.
The Hidden Wiki, in particular, serves as a gateway to various websites that offer illegal goods and services, such as drugs, weapons, counterfeit documents, and even human trafficking. By accessing the Hidden Wiki, you may inadvertently stumble upon explicit pornography, disturbing images, or even illegal forums discussing criminal activities.
It’s crucial to understand that engaging with illegal content can have serious legal consequences. Authorities actively monitor illegal activities on the Deep Web, and your involvement, even as a mere visitor, can put you at risk of being targeted for investigation or prosecution.
Therefore, it’s essential to exercise caution and avoid accessing the Hidden Wiki or any other websites that may contain illegal content.
Potential for Cyberattacks
By accessing the Hidden Wiki on the Deep Web, you open yourself up to the potential for cyberattacks, posing significant risks to your online security and personal information.
The Hidden Wiki is a platform where users can find links to various websites, some of which may be malicious or compromised. These websites can contain malware, ransomware, or phishing schemes that are designed to steal your sensitive data or gain unauthorized access to your devices.
Cybercriminals often target users on the Deep Web due to the anonymity it provides, making it difficult to trace their activities. Additionally, the Hidden Wiki itself may be controlled by hackers who can manipulate the links and direct users to malicious websites without their knowledge.
Therefore, it’s crucial to exercise caution and implement robust security measures when accessing the Hidden Wiki to protect yourself from cyberattacks.
Illegal Activities and Content
When accessing the Hidden Wiki on the Deep Web, you need to be aware of the prevalence of criminal marketplaces. These platforms facilitate illegal activities such as drug trafficking, weapons trade, and hacking services.
Moreover, the decentralized nature of the Deep Web poses challenges for content censorship, making it easier for illicit materials like child pornography and counterfeit goods to circulate.
It’s crucial to understand that engaging in illegal activities on the Deep Web can have severe legal consequences, including potential criminal charges and prosecution.
Criminal Marketplace Prevalence
Criminal marketplaces abound on the Deep Web, where illegal activities and content are readily available for those who seek them. These marketplaces serve as hubs for a wide range of criminal activities, including the sale of drugs, weapons, counterfeit goods, stolen data, and hacking services.
The anonymity and encryption provided by the Deep Web make it an attractive platform for criminals to conduct their illicit business without being easily traced or detected by law enforcement agencies.
The prevalence of criminal marketplaces on the Deep Web poses a significant challenge for authorities in their efforts to combat cybercrime.
It’s important for individuals to be aware of the risks associated with these marketplaces and to take precautions to protect themselves from getting involved in illegal activities or becoming victims of cybercrime.
Content Censorship Challenges
The prevalence of criminal marketplaces on the Deep Web not only poses a significant challenge for authorities but also brings forth the content censorship challenges surrounding illegal activities and content.
One of the main concerns is the difficulty in monitoring and removing illegal content from the Deep Web. The decentralized nature of the Deep Web makes it challenging for authorities to track down and shut down websites promoting illegal activities, such as drug trafficking, weapons trading, and human trafficking.
Additionally, the use of encryption and anonymizing tools further complicates the process of identifying and removing such content. This poses a risk as it allows illegal activities to flourish and potentially harm individuals.
Efforts are being made to develop advanced technologies and strategies to combat these content censorship challenges, but it remains an ongoing battle.
Legal Consequences for Users
Engaging in illegal activities or accessing illegal content on the Deep Web can have severe legal consequences for users. The Deep Web, with its anonymity and lack of regulation, may attract individuals seeking to participate in illicit activities. However, it’s important to understand that law enforcement agencies actively monitor the Deep Web, and they can track down users engaging in illegal activities. If caught, you could face criminal charges, hefty fines, and even imprisonment.
The Deep Web is home to various illegal activities such as drug trafficking, human trafficking, hacking, and the sale of illegal goods and services. Furthermore, accessing illegal content like child pornography can result in severe legal repercussions. It’s crucial to remember that engaging in any illegal activity, regardless of the platform, isn’t only morally wrong but also carries significant legal risks.
Malware and Cyber Attacks
It’s crucial to stay vigilant and take appropriate precautions to protect yourself from the risks of malware and cyber-attacks. The Deep Web can be a breeding ground for malicious activities, as it provides anonymity and a platform for cybercriminals to carry out their nefarious actions.
Malware, short for malicious software, is a common threat in this realm. It can infect your device and steal sensitive information, such as passwords or financial details. Cyber-attacks, on the other hand, can range from phishing scams to Distributed Denial of Service (DDoS) attacks aimed at disrupting websites and networks.
It’s important to have robust security measures in place to safeguard against these threats. Ensure that your antivirus software is up to date and regularly scan your device for any potential malware. Be cautious when clicking on links or downloading files from the Deep Web, as they may contain harmful content.
It’s advisable to use a virtual private network (VPN) to encrypt your internet connection and protect your identity. Additionally, never share personal or financial information on the Deep Web, as it can easily fall into the wrong hands.
Law Enforcement and Surveillance
Law enforcement agencies and surveillance play a significant role in monitoring and investigating activities on the Deep Web. These agencies are constantly working to detect and disrupt illegal activities, such as drug trafficking, weapons sales, and child exploitation, that occur in the hidden corners of the internet. Through various techniques, law enforcement agencies gather intelligence and gather evidence to build cases against individuals or groups involved in criminal activities on the Deep Web.
In order to carry out their duties effectively, law enforcement agencies employ a variety of surveillance methods. They may use advanced technologies to monitor online communications, track IP addresses, and infiltrate criminal networks. Additionally, collaboration between different agencies, both national and international, is crucial in combating criminal activities on the Deep Web. By sharing information and resources, law enforcement agencies can better identify and apprehend individuals involved in illegal activities.
However, it’s worth noting that law enforcement agencies face challenges in their efforts to combat criminal activities on the Deep Web. The anonymous nature of the Deep Web, coupled with encryption techniques and the use of virtual currencies, can make it difficult to trace and apprehend individuals involved in illegal activities. Furthermore, the constant evolution of technology and the ability of criminals to adapt and innovate pose ongoing challenges for law enforcement agencies.
Protecting Your Identity and Privacy
As you navigate the Deep Web, safeguarding your identity and protecting your privacy becomes paramount in light of the challenges law enforcement agencies face in combating criminal activities. The Deep Web is a haven for illegal activities, and without taking proper precautions, your personal information could be at risk.
There are several steps you can take to protect your identity and maintain your privacy.
First and foremost, it’s crucial to use a reliable VPN (Virtual Private Network) service. A VPN encrypts your internet connection, making it nearly impossible for anyone to track your online activities. Additionally, it’s advisable to use a secure browser such as Tor, which not only hides your IP address but also provides access to hidden services on the Deep Web.
Furthermore, using strong, unique passwords for every online account is essential. Consider using a password manager to generate and store complex passwords securely. Avoid sharing personal information or using real names in any online communication or forum on the Deep Web.
Lastly, regularly updating your antivirus software and keeping your operating system up to date will help protect against potential security vulnerabilities.
Precautions for Navigating the Deep Web
When navigating the Deep Web, it’s crucial to take precautions to ensure your safety and protect your privacy.
The anonymity of the Deep Web makes it a breeding ground for illegal activities, scams, and malware.
To safeguard yourself, start by using a reliable VPN (Virtual Private Network) to mask your IP address and encrypt your internet traffic. This will make it harder for anyone to track your online activities.
Additionally, consider using a secure and private browser like Tor, which is specifically designed to protect your identity and keep your browsing history confidential.
It’s also important to keep your operating system and antivirus software up to date to prevent any potential vulnerabilities from being exploited.
Remember never to share personal information or engage in any illegal activities while on the Deep Web.
Lastly, be cautious when accessing unknown websites or links, as they may contain harmful content.
Staying Safe on the Hidden Wiki
It’s essential to take certain precautions to ensure your safety and protect your privacy while navigating the Hidden Wiki.
The Hidden Wiki is a part of the deep web that contains various websites, some of which may be illegal or dangerous.
First and foremost, make sure to use a reliable and secure VPN (Virtual Private Network) to hide your IP address and encrypt your internet connection. This will help protect your anonymity and prevent anyone from tracking your online activities.
Additionally, it’s crucial to keep your software and antivirus programs up to date to defend against potential malware or hacking attempts.
When accessing the Hidden Wiki, be cautious of the links you click on. Stick to websites that are well-known and trusted, as clicking on unknown links can lead to malicious websites or scams.
Remember never to disclose personal information or engage in any transactions that seem suspicious.
Lastly, if you ever come across illegal content or activities, report them to the appropriate authorities.
FAQs
Q. How Can I Access the Hidden Wiki and the Deep Web?
To access the hidden wiki and the deep web, you can use a Tor browser. It allows you to browse anonymously and access websites not indexed by search engines. Be cautious of the risks involved.
Q. Are There Any Legal Uses for the Hidden Wiki and the Deep Web?
Yes, there are legal uses for the Hidden Wiki and the deep web. It can be a valuable resource for accessing information anonymously or for researchers who need to gather data without censorship.
Q. What Are the Potential Consequences of Accessing Illegal Activities or Content on the Hidden Wiki?
Accessing illegal activities or content on the Hidden Wiki can have severe consequences. You may face legal repercussions, such as criminal charges or imprisonment. Additionally, you risk exposing yourself to dangerous individuals who could harm you physically or financially.
Q. How Can I Protect Myself Against Malware and Cyber Attacks While Browsing the Hidden Wiki?
To protect yourself from malware and cyber-attacks while browsing the hidden wiki, make sure to keep your antivirus software up to date, avoid clicking on unknown links, and use a VPN for added security.
Q. What Are the Risks of Law Enforcement and Surveillance While Using the Hidden Wiki?
Law enforcement and surveillance pose risks when using the Hidden Wiki. They can monitor your activities and potentially identify you. It’s important to take precautions, like using VPNs and encrypted messaging, to protect your anonymity.
Conclusion
In conclusion, navigating the Hidden Wiki on the Deep Web comes with significant risks and precautions. Engaging in illegal activities and encountering malware and cyber-attacks are genuine concerns. Additionally, law enforcement and surveillance pose threats to your privacy and identity.
In order to stay safe, it’s crucial to take precautions, such as using a VPN Tor browser and maintaining anonymity. Remember, the Deep Web can be a dangerous place, so always prioritize your safety and protect yourself online.
The post Understanding the Hidden Wiki Onion: Risks and Precautions appeared first on TheHiddenWiki.
]]>In this digital world, all the important things are on our smartphones and computers. In this era of technology, privacy and security are the major concerns of most internet users. The websites and applications require user personal information, like name, phone number, and email address, to access their sites. However, these requirements are simple and […]
The post A Similar Hack as on Friendtech Would Not Affect Hidden Wiki Visitor appeared first on TheHiddenWiki.
]]>In this digital world, all the important things are on our smartphones and computers. In this era of technology, privacy and security are the major concerns of most internet users. The websites and applications require user personal information, like name, phone number, and email address, to access their sites. However, these requirements are simple and easy to fulfill.
In this digital world, all the applications and websites are not hundred percent secure, which means your data is not secure. On the Internet, there are a lot of people; some are good, and some are evil. Nowadays, many crimes are committed on the Internet, such as hacking, scamming, and stealing money from bank accounts and crypto wallets.
Recently, FriendTech, the social crypto application, was launched, and it created hype in the crypto market as well as on all social media platforms. In the very first week after its launch, more than 100,000 users joined Friend Tech. However, this application is not free to use; you must pay to create an account. Most people know about this application after the SIM-Swap attack.
Recently, Friendtech has been on hackers’ radar. The app itself is not completely hacked, but the accounts of users were hacked by their phone numbers. In this attack, hackers hacked their accounts and stole Ethereum. After this attack, users are scared to use Friend tech and deposit ETH. It is not the solution to avoid the use of Friend tech. In this article, we will guide you on how you can use friendtech on the hidden wiki without getting any threat of a hack.
The Hidden Wiki
The Hidden Wiki is a directory of the dark Web that allows people to visit different sites without any security threat. It is one of the best sites on the dark Web, and most people call the Wikipedia of the dark Web. But why the hidden Wiki is so famous among all the dark net websites? Here are some main reasons why the hidden Wiki is the most trusted and popular directory.
Here are some reasons why Hidden Wiki is popular and people’s first choice to find onion links. First of all hidden wiki interface is simple and understandable, while other platforms’ interfaces are complicated. On this site, all the onion links are categorized, which means you don’t need to do a lot of searches to find your desired website.
You don’t need to reveal your identity to use any platform. You can submit any post or comment anonymously. The Hidden Wiki is full of good and bad stuff, and where people decide what they want to explore. Some people think hidden Wiki is illegal to use. Therefore, hidden Wiki is not illegal to visit, but some links they provide are indeed illegal.
Moreover, you cannot visit Hidden Wiki on simple browsers like Google Chrome, Firefox, and Bing. To access Hidden Wiki, you need to install Tor Browser.
Tor browser
Tor is a browser that gives access to the dark Web. It offers browsing without any privacy risk or threat. Like other browsers, it saves your passwords and history notes your browsing and gives relevant ads. Tor browser has an encryption method, which means it does not save your history or passwords.
How To Use Hidden Wiki Through Tor Browser?
First, you have to download the Tor browser on your computer or any other device where you want to run Hidden Wiki. For security purposes must download the VPN and turn it on. Open the Tor browser; it requires a security setting where three options are on the list: standard, safe, or safest. Select Safest to prevent any security threat.
Once you are on the Tor browser, you have turned on all the security settings and the VPN. Now it’s time to explore Hidden Wiki. DUCKDUCKGO is the search engine of the Tor browser. On this search engine, type Hidden Wiki; on the top results, you will find the official Hidden Wiki Website.
The Hidden Wiki is the top directory of the dark Web that provides all the Onion websites. Furthermore, you can search for what type of websites you are looking for. Remember that there are fake and scam websites on hidden Wiki, too. Be careful when you visit any site any of them.
Do you Know About Friend Tech?
Friendtech is a new decentralized social media app with crypto market features like airdrop, rewards, fee sharing, and much more. This decentralized app connects with Twitter(X).it is the most beneficial application for influencers, celebrities, and crypto investors. Users buy shares of any influencer account and chat with them privately.
Later, Friend Tech changed the name shares to keys. Everyone buys keys to communicate with each other. With keys, people have access to private chat rooms in-app and exclusive content from the X (Twitter) user.
On this app, every user has a chat group, just like the groups in Telegram. In order to enter the other person’s private chats, first must purchase keys. This group is the same as stocks, and their share price depends on the community; the higher the group members higher the share price.
Joining groups is a profitable investment in Friend Tech. However, Friend Tech launched airdrop features to engage their users. In the airdrop, friend tech gives rewards for completing tasks.
To participate in the airdrop, go to your account and click on the airdrop option, where you will find your task list to avail of the airdrop. Usually, on airdrop, the main task is referring your invite code to your friend. When your friend adds your invite code to join this platform, friend tech gives you rewards points.
Note: Every person who wants to join Friend Tech must have an X account, 0.01 ETH, and, most importantly Friend Tech invite code.
How to Download the Friend Tech App
Friend tech is a social media app, and it is easy to install like other applications. To download this application on your mobile phone, follow these simple steps.
- Go to any browser and visit FriendTech.
- Tap on the menu in the top right corner of your browser, and click Install App.
- Allow the download to complete.
- You can access the application just clicking on the friend tech icon from the application list.
Now you have downloaded the application, it’s time to create an account with friend tech.
How to Sign in FriendTech
- To create an account, click on sign in.
- Enter your mobile number. Instead of using a mobile number, you can use a Google account or Apple account.
- Enter the friend tech invite code.
- Link your X(Twitter) account to confirm your identity.
- Now, deposit 0.01 ETH in your account. Friend tech provides two ways to deposit funds in your account: Deposit on Mainnet and Receive on base.
- Deposit mainnet: you can send ETH directly to your Friend tech wallet.
- Receive on base: Send Ethereum to the provided address on the base network.
- Choose the base option to deposit successfully. In case of any inconvenience, your direct deposit of funds may be lost.
- After all the procedure is completed, you are able to explore and trade shares on the platform.
Why is Friend Tech so Popular?
Friend tech combines social media with stock market elements. Users can invest in other user profiles with keys and their value increases as they grow in popularity. Friend Tech is the fastest-growing crypto-social platform.
This decentralized application launched on August 10, 2023; after its launch, more than 100,000 users joined this platform. The friend tech has generated more than 25$ million in fees in one week.
However, when a key is sold or purchased, a 5% fee goes to the app, and the other 5% goes to the group owner. Moreover, the price of keys depends on group popularity. Where the group has more members, the price of their key is high.
Friend Tech is Under SIM-Swap Threats
A new wave of SIM-Swap heists where scammers access users’ friend tech accounts and steal their liquidity. In this recent attack, hackers stole around $400,000 worth of Ethereum. Several influencer accounts on the crypto-social platform claimed that their account was hacked and attackers were draining Ethereum from their wallets.
However, friend Tech was not directly hacked, and the hackers attacked individual user’s accounts by hijacking their phone numbers. SIM-Swapping is when hackers gain control of a user’s phone number and use it to access their Cryptocurrency wallets.
On the other hand, Friend Tech introduced a new login method to help prevent SIM-Swap attack account takeovers. However, security experts said this method is not enough, and Users should use Two-factor authentication to protect themselves better.
Using FriendTech on the Hidden Wiki
In this digital era, all things are now in our hands. Cryptocurrency has gained popularity all over the world with its satisfactory results. By using Cryptocurrency, it is easy to make transactions without third-party involvement. Cryptocurrency gives great benefits to its users. On the market, there are several marketplaces to buy and sell digital currencies.
However, Cryptocurrency gives financial strength, but the question in mind many investors is what is the best secure platform to invest in. On the Internet, there are a lot of platforms that claim they are highly secure.
In August 2023, 0xRacerALT and Shrimppepe introduced the social-crypto platform to socialize and trade your shares and earn a percentage of transaction fees. However, Friend Tech has been highly popular among all the crypto marketplaces after its launch. Additionally, the platform gives several benefits to its users, but after the SIM-Swap attack, user’s major concern is the privacy and security of their accounts wallet.
As I mentioned above, friend Tech changed its login method to prevent scams, but that is not enough to secure your account. All the security concerns people are scared about using Friend tech.it is a great platform to communicate with others and earn ETH.
Most people are scared and decide to leave the platform after the SIM-Swap threat. Instead of leaving the platform, why not use the most secure hack to save your account and secure your wallet? The Hidden Wiki is the key to securing your account completely from attackers.
The Hidden Wiki is a website on the dark Web where you use all the platforms without showing your identity. Firstly, register yourself on Hidden Wiki and use any platform anonymously. It is a simple step to follow to avoid scams; using FriendTech through Hidden Wiki makes you safe from attackers.
Final Words
The newly launched decentralized application is in a town where people use social media combined with the crypto market. Friend Tech is one of the leading web3 apps among all the crypto and social media platforms. In this article, I mentioned all the steps on how you can download and create an account on friend tech.
The recent SIM-Swap attack on friend tech users is more concerned about the privacy and liquidity of your account. However, to get rid of these types of hacks and save your money from hackers, follow this trick to use friendtech through Hidden Wiki safely. It is one of the safest ways to use your Friend tech account more securely and prevent from SIM-Swap attack.
FAQS
where can I get the Friend Tech invite code?
You can get an invite code from your friends who already have a friend tech account. Moreover, you can also check on Twitter and other social media platforms where people share their invitation codes.
Which Cryptocurrency is used in Friend Tech?
Friend tech built on Ethereum (ETH) layer two blockchains called base.
How much is 0.01 ETH in dollars?
Cryptocurrency prices are unpredictable. No one knows how much you pay for 0.01 Ethereum at the time when you purchase the token. Today, the cost of 0.01 Ethereum is 16$.
The post A Similar Hack as on Friendtech Would Not Affect Hidden Wiki Visitor appeared first on TheHiddenWiki.
]]>